Is Signal Safe? Encryption Behind Messaging Apps
Updated April 2026
Quick Verdict: Is Signal Safe?
Yes — for personal use, Signal is the most secure mainstream messaging app available. Its end-to-end encryption, open-source codebase, and minimal data collection make it the gold standard among privacy-focused tools. However, “safe” is not unconditional: Signal’s security depends heavily on device integrity, user behavior, and your specific threat model.
|
Question |
Short Answer |
|---|---|
|
Are messages encrypted end-to-end? |
✅ Yes, always — no exceptions |
|
Can Signal employees read your messages? |
❌ No — technically impossible |
|
Does Signal sell your data? |
❌ No — nonprofit, no advertisers |
|
Is Signal truly anonymous? |
⚠️ Partial — phone number required |
|
Is it safe for classified government use? |
❌ No — not designed for that purpose |
|
Is it safe for journalists and activists? |
✅ Yes — widely recommended by experts |
|
Can it be hacked? |
⚠️ Only via device compromise, not the protocol |
Insight #1 — Measurable threshold
Signal’s security holds as long as your device hasn’t been compromised. If you are running a fully up-to-date OS with no stalkerware installed, and your contacts do the same, the probability of your message content being exposed via the Signal Protocol itself is effectively zero under current cryptographic standards. The risk shifts entirely to the endpoint layer (your phone, your contacts’ phones) — not the app.
Understanding What Signal is Exactly?
Product: Signal
|
Property |
Details |
|---|---|
|
Category |
Encrypted instant messaging app |
|
Platform |
iOS, Android, Windows, macOS, Linux |
|
Developer / Brand |
Signal Foundation (nonprofit) & Signal Messenger LLC |
|
Encryption protocol |
Signal Protocol (also adopted by WhatsApp, Google Messages RCS, and formerly Skype) |
|
Business model |
Donations + Signal Sustainer subscriptions — no advertising |
|
User base |
~70 million active users |
Signal is a free, open-source messaging application that lets users exchange texts, voice notes, images, files, and make audio/video calls — all protected by default end-to-end encryption. It was co-founded by cryptographer Moxie Marlinspike and WhatsApp co-founder Brian Acton, who has loaned the Signal Foundation over $100 million toward its long-term development.
Signal’s Core Security Features — Summary Table
|
Security Feature |
What It Does |
Status |
|---|---|---|
|
End-to-end encryption (E2EE) |
Encrypts all messages, calls, files on sender’s device; only recipient can decrypt |
✅ On by default, no opt-out |
|
Signal Protocol |
Gold-standard cryptographic protocol with forward secrecy + post-compromise security |
✅ Independently audited |
|
Sealed Sender |
Hides the sender’s identity from Signal’s own servers |
✅ Active |
|
Safety Numbers |
Cryptographic fingerprints to verify you’re speaking to the right person |
✅ Available, manual |
|
Disappearing Messages |
Auto-deletes messages from both devices after a set timer |
✅ Optional, user-configurable |
|
Registration Lock (PIN) |
Prevents account takeover if phone number is compromised or SIM-swapped |
✅ Optional (recommended on) |
|
Screen Security |
Blocks message previews in app switcher, disables screenshots in-app |
✅ Optional |
|
Note to Self |
Encrypted personal notepad — not shared with anyone |
✅ Included |
|
Incognito Keyboard |
Prevents the keyboard from learning your typing patterns |
✅ Optional |
|
Open-source code |
Full codebase publicly reviewable on GitHub |
✅ Yes |
Now, let’s stop and discuss Signal’s security system in more detail.
End-to-end Encryption
As previously mentioned, Signal utilizes end-to-end encryption, provided by a proprietary protocol, as one of its main methods of protection. With this type of information processing, encryption and decryption occur on the devices of users. It is important to note that the data remains encrypted until it reaches its destination.
After encryption, the information looks like a set of unrelated characters. That is why, even if attackers intercept your message, they will not be able to gain anything from it. Images, videos, and other files that you want to share with your interlocutor are also encrypted.
Signal was ahead of many applications by creating its own protocol that implements end-to-end encryption. Large companies such as Microsoft, Google, and Facebook now use it to ensure the security of their solutions.
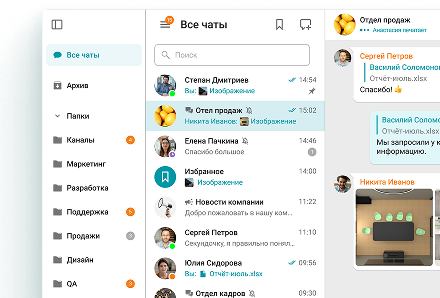
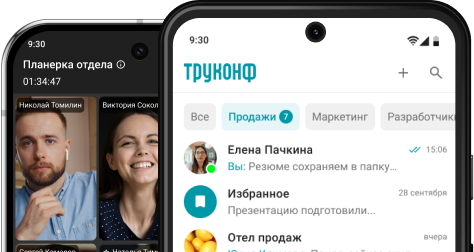
Your Messages Are Secure with TrueConf!
A powerful self-hosted video conferencing solution for up to 1,000 users, available on desktop, mobile, and room systems. Your confidential information is protected by 12 levels of security.
Signal Security Numbers
As another protective measure, Signal utilizes a security number. Each chat has a unique number, so you can confirm it with your interlocutor to ensure its authenticity.
It is especially important to be confident in another user when discussing confidential information.
If the interlocutor changes devices or reinstalls the application during the conversation, you will be immediately notified. This feature is specifically designed to protect against «Man-in-the-Middle» (MITM) attacks, in which a hacker disguises themselves as another user to obtain sensitive data.
In the event of a mismatch of security numbers or a notification of an unexpected device change, you should contact Signal Support to ensure your protection and prevent potential leaks.
Open-source
Signal has a decentralized model and open-source code, allowing any developer to modify the technology and share it. The main goal, as stated by the creators of the app, is to disseminate knowledge.
However, this does not mean that the Signal code is simplistic and unreliable. In October 2016, researchers from Queensland University of Technology, Oxford and McMaster University published a conclusion confirming the cryptographic security of the solution.
What Personal Data Does Signal Collect?
Signal stores the absolute minimum data required for the service to function. Unlike most messaging platforms, it has no advertising model and no commercial incentive to collect behavioral data.
According to Signal’s privacy policy, the only personal information stored server-side is:
-
Your phone number (required for account registration)
-
Your account creation date
-
The date you last connected to Signal
All message content, media, contacts, call history, group memberships, and profile information are either end-to-end encrypted (meaning Signal cannot read them) or stored only on your device. When you send a message, it is temporarily stored on Signal’s servers only until delivery — and in encrypted form that Signal’s own team cannot read.
Privacy nuance: Google Maps API
Signal uses the Google Maps API to handle location data, which passes metadata including your IP address to Google’s infrastructure. For a privacy-first app, this is a notable inconsistency — open-source map alternatives like OpenStreetMap exist and are not used. Users who share their location via Signal should be aware of this data path.
Known Limitations and Real-World Risks
Signal’s encryption is cryptographically sound — but the app is not risk-free in every scenario. Understanding where the protection ends is essential to using it safely.
💡 Insight #2 — Measurable condition
A 2025 academic paper demonstrated that delivery receipts in Signal (and WhatsApp, Threema) can be exploited to expose behavioral metadata — not message content, but patterns such as when you are online, asleep, or switching devices. This attack works by sending specially crafted invisible interactions that trigger silent delivery receipts. The risk is present even with disappearing messages enabled, because it operates at the network-timing layer, not the content layer.
|
Risk Category |
Description |
Mitigation |
|---|---|---|
|
Phone number requirement |
Your account is linked to a real phone number, which is subpoenable and SIM-swappable |
Use a VoIP or Google Voice number; enable Registration Lock |
|
Device compromise |
If your phone is hacked, attackers can read messages directly on-screen regardless of encryption |
Keep OS updated; use full-disk encryption; avoid sideloading apps |
|
Endpoint trust |
Your contacts’ devices are equally critical — their compromise exposes your shared conversation |
Verify safety numbers with sensitive contacts |
|
No cloud backup by default |
Messages are stored on-device only; losing your phone means losing your messages |
Create an encrypted local backup before switching devices |
|
Delivery receipt metadata |
Timing patterns of receipts can reveal online/offline behavior without exposing content |
Disable read receipts in Settings > Privacy |
|
US infrastructure (AWS) |
Signal’s servers run on Amazon Web Services, subject to US legal process |
Signal cannot technically comply with content requests — but metadata requests are theoretically possible |
|
Not suitable for classified communication |
Signal is not designed for FOIA compliance or classified data handling |
Use officially accredited government communication systems for classified work |
|
Accidental group additions |
The “Signalgate” incident (2025) showed that user error — not technical failure — remains a real risk |
Carefully verify group members before sharing sensitive information |
The “Signalgate” Incident: What It Actually Means for Security
In early 2025, a high-profile incident involving US national security officials drew global attention to Signal. Senior advisors, including National Security Advisor Mike Waltz, accidentally added Jeffrey Goldberg — editor-in-chief of The Atlantic — to a Signal group chat discussing sensitive military operations.
The crucial point: Signal’s encryption was not breached. The incident was entirely a user error — a wrong contact was added to a group chat. The CIA Director later testified that the CIA actively uses Signal for day-to-day internal communication. The episode illustrates a universal security principle: no cryptographic protocol can protect against trusting the wrong person. Signal is “secure by default,” but it cannot make access control decisions on behalf of its users.
Disadvantages Of Using Signal App
Despite its strong security posture, Signal has practical limitations that make it unsuitable for some use cases.
-
Smaller user base than mainstream apps. With approximately 70 million active users, Signal is dwarfed by WhatsApp (~2 billion) and Telegram (~900 million). If your contacts don’t use Signal, the benefit of its encryption disappears for those conversations.
-
No multi-device synchronization by default. Signal ties your account to a primary smartphone. While desktop and tablet clients exist, they function as extensions of the mobile app — your phone must remain connected for the desktop version to work correctly. Users who regularly switch between devices find this friction significant.
-
No message history backup to cloud. Because Signal stores everything on-device by default and doesn’t sync to a cloud server, switching phones without a manual backup means losing all message history. This is a feature for privacy, but a practical inconvenience for most users.
-
Limited business and enterprise functionality. Signal does not support admin-managed multi-user channels, third-party integrations, compliance logging, or the kind of audit trail that regulated industries require. It is not positioned as a business communication platform.
-
The 2022 Twilio data breach. In 2022, a cyberattack on Signal’s SMS verification provider Twilio exposed the phone numbers of approximately 1,900 users. Attackers used this data to re-register accounts and attempt fraud impersonation. The breach did not compromise any message content — the encryption remained intact — but it highlighted the vulnerability of the phone-number-based identity model.
Signal vs. Main Competitors
Messaging App Security Comparison
|
Feature |
Signal |
|
Telegram |
TrueConf |
|---|---|---|---|---|
|
End-to-end encryption |
✅ Always on |
✅ Always on |
⚠️ Secret Chats only |
✅ Always on |
|
Metadata collected |
Minimal (phone number, last seen) |
Extensive (contacts, behavior, device info) |
Moderate (stored on servers) |
On-premises, admin-controlled |
|
Open-source |
✅ Full |
❌ Client only |
⚠️ Partial |
✅ Auditable |
|
Cloud backup of messages |
❌ No (device only) |
⚠️ Optional, may be unencrypted |
✅ Yes (server-stored) |
Self-hosted — admin decides |
|
Corporate/business features |
❌ Limited |
⚠️ Basic channels |
✅ Channels, bots |
✅ Full enterprise suite |
|
On-premises deployment |
❌ No |
❌ No |
❌ No |
✅ Yes |
|
Data sovereignty |
❌ US-based (AWS) |
❌ Meta infrastructure |
❌ Dubai-based servers |
✅ Deploy in your own network |
|
Regulatory compliance (GDPR, etc.) |
⚠️ Limited control |
⚠️ Meta policies apply |
⚠️ Limited |
✅ Full admin control |
|
Phone number required |
✅ Yes |
✅ Yes |
✅ Yes |
❌ No |
TrueConf
Thanks to its multi-level protection system, TrueConf is already being used by government and law enforcement agencies in many countries. TrueConf solution utilizes methods such as working on a single port, access control, and data storage on-premises, making potential data leaks almost impossible.
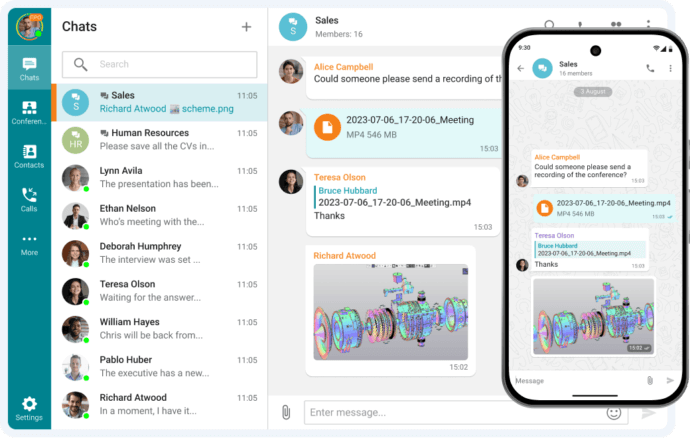
TrueConf not only enables safety messaging, but also audio and video conferencing with the ability to use collaboration tools, such as presentation showing, content sharing, remote desktop management, and much more.
Of particular interest to many are the advanced features based on Artificial Intelligence, which allow one to use TrueConf even in the most adverse conditions. This feature is provided by both smart noise reduction and background blurring, guaranteeing absolute privacy for communication.
Take your team communication to the next level with TrueConf!
A powerful self-hosted video conferencing solution for up to 1,000 users, available on desktop, mobile, and room systems.
The main reasons for WhatsApp’s popularity among businessmen are its ability to create working channels and its large user base. At the same time, you can make audio and video calls, and share various types of files, from images to documents.
WhatsApp employs end-to-end encryption for security, just like Signal. However, many potential users are confused by the amount of personal information that Meta collects without the ability to make a ban.
Telegram
Another application that is gaining increasing popularity among business representatives is Telegram. The application’s extensive capabilities, including not only audio and video communication but also channels with an unlimited number of subscribers, have already attracted a large number of regular users.
However, not everything is good with Telegram’s privacy, despite the apparent security of the solution. The application uses encryption at the transport layer, but it is not end-to-end. This means that Telegram IT specialists can read your messages at any time, regardless of the type of сhat. What’s even more worrying is the fact that the solution stores all user data on its servers, ultimately making privacy a mirage.
How to Maximize Your Security on Signal
The following settings should be configured by any user who relies on Signal for sensitive communications.
-
Enable Registration Lock (Settings → Account → Registration Lock). Requires your Signal PIN to register your phone number on a new device. Prevents SIM-swap account takeovers.
-
Enable Screen Security (Settings → Privacy → Screen Security). Hides message content in the app switcher and prevents screenshots inside the app.
-
Set disappearing messages as default for new conversations (Settings → Privacy → Default Timer). Messages are deleted from both devices after your chosen interval.
-
Disable read receipts (Settings → Privacy → Read Receipts). Reduces metadata leakage from delivery receipt timing analysis.
-
Use a strong, alphanumeric Signal PIN. Signal uses secure enclaves to limit brute-force attempts, but a strong PIN adds a critical layer of protection for your registration lock and encrypted backup.
-
Verify Safety Numbers with any contact you share sensitive information with. Do this in person or via a secondary trusted communication channel.
-
Keep Signal and your device OS updated. Protocol-level security is sound, but device-layer vulnerabilities are the primary real-world attack vector.
-
Use a non-personal phone number if anonymity is required (VoIP number or Google Voice). Signal itself does not offer anonymous registration.
💡 Insight #3 — Measurable condition
Enabling Registration Lock reduces the risk of account hijacking via SIM-swap to near zero for the duration of the 7-day waiting period Signal enforces after a failed PIN attempt. If an attacker has your SIM but not your PIN, they cannot complete re-registration for at least 7 days — giving you time to detect the attack and contact your carrier. Without Registration Lock, SIM-swap account takeover can be completed in under 10 minutes.
Who Should (and Shouldn’t) Use Signal
Signal is the right choice if you are:
-
An individual who wants private messaging without technical complexity
-
A journalist, activist, or researcher communicating with sources
-
Someone concerned about data collection by platforms like Meta or Google
-
A small team that needs secure, ad-free communication
-
A government official conducting non-classified internal communications
Signal is not the right choice if you need:
-
Legal compliance or message archiving (FOIA, financial recordkeeping, eDiscovery)
-
Discussion of classified or sensitive government/military information
-
Enterprise features: admin controls, integrations, SSO, compliance dashboards
-
A platform your entire user base already uses (Signal’s adoption is much lower than WhatsApp or iMessage)
-
On-premises deployment for data sovereignty in regulated industries
The Bottom Line. Is Signal right for you?
Signal stands out from other communication applications due to its wide range of features and reliable user data protection system. The main goal of the solution is to create a safe space for people to discuss any topic and share necessary files.
Thus, Signal will appeal to those users who want to communicate freely while feeling completely secure from any invasions of their personal data.
However, this solution is not suitable for businesses due to security-related restrictions. If you are looking for a solution for corporate interaction, then it is much better to turn to TrueConf.
FAQ
Is Signal safe to use in general?
Yes. Signal is widely considered the most secure consumer messaging app available. It uses end-to-end encryption by default for all messages, calls, and media — meaning neither Signal, your ISP, nor any third party can read your communications. Its code is open-source and has been independently audited multiple times. For everyday private communication, it is safe.
Can the government or police access Signal messages?
No — not through Signal. Because of end-to-end encryption, Signal does not store message content and technically cannot provide it to law enforcement even under a court order. When served with legal demands, Signal can only provide a phone number and account creation/last-seen dates. To access Signal messages, authorities would need physical access to an unlocked device.
Was Signal hacked? What happened with “Signalgate”?
Signal’s encryption was not hacked. In 2025, a US national security official accidentally added a journalist to a secure Signal group chat discussing military operations. The incident was entirely a user error — the wrong person was added to a group — and demonstrated a social/operational security failure, not a technical one. Signal’s cryptography remained intact throughout.
Is Signal better than WhatsApp for privacy?
Yes, meaningfully so. Both use the Signal Protocol for message encryption. However, WhatsApp is owned by Meta and collects extensive metadata — contact graphs, usage patterns, device identifiers — which feeds Meta’s advertising systems. Signal collects only your phone number, account creation date, and last-seen date. Signal also does not allow Meta-style content moderation review of flagged messages.
Is Signal truly anonymous?
Partially. Signal requires a valid phone number to register, which can be linked back to you via your carrier or a subpoena. Your display name and profile photo are encrypted and not visible to Signal’s servers, and the “Sealed Sender” feature hides sender identity from Signal’s infrastructure. But your phone number creates a non-anonymous identity anchor. For full anonymity, alternatives like Session (which uses no phone number) exist, though they sacrifice features and ease of use.
Is Signal safe for business use?
For small teams and informal secure communication, Signal works well. For enterprises with compliance requirements — message archiving, SSO, admin controls, audit logs, data residency obligations — Signal is not appropriate. It lacks admin dashboards, has no third-party integrations, and its privacy design actively prevents the kind of logging that regulated industries require. Enterprise teams should evaluate on-premises solutions like TrueConf.
What are Signal’s biggest security weaknesses right now?
Signal’s weakest points are: (1) the phone number requirement, which creates a subpoenable identity anchor and SIM-swap vulnerability; (2) device-layer risk — if your phone is compromised by malware, encryption doesn’t protect messages visible on screen; (3) behavioral metadata leakage via delivery receipt timing (demonstrated in a 2025 academic paper), which can reveal when you are online without exposing message content; and (4) its US infrastructure (AWS), which is subject to US legal process, even if the content cannot technically be accessed.
About the Author
Nikita Dymenko is a technology writer and business development professional with more than six years of experience in the unified communications industry. Drawing on his background in product management, strategic growth, and business development at TrueConf, Nikita creates insightful articles and reviews about video conferencing platforms, collaboration tools, and enterprise messaging solutions.








Follow us on social networks