How Secure Is WhatsApp?
Updated April 2026
Executive Summary: The Short Answer on WhatsApp Security
WhatsApp provides end-to-end encryption for messages in transit, which protects content from interception during delivery. However, for business and enterprise use, critical gaps remain: unencrypted cloud backups, extensive data collection by Meta, limited administrative controls, and non-compliance with strict data governance frameworks like GDPR.
For personal, informal communication, WhatsApp’s security model is generally sufficient when users enable two-factor authentication and manage backups carefully. For corporate environments handling sensitive data, regulated industries, or teams requiring audit trails and centralized governance, a purpose-built secure platform offers significantly stronger protection and control.
Quick Security Assessment at a Glance
|
Security Dimension |
WhatsApp (Consumer) |
Enterprise Requirements |
Gap Analysis |
|---|---|---|---|
|
Message Encryption |
End-to-end (Signal protocol) |
End-to-end + at-rest encryption |
Backups stored unencrypted in cloud |
|
Data Ownership |
Meta collects metadata & usage data |
Full data sovereignty required |
No opt-out from Meta data processing |
|
Admin Controls |
None for business accounts |
User provisioning, access policies, audit logs |
Cannot enforce security policies centrally |
|
Compliance |
Limited GDPR alignment |
Full GDPR, HIPAA, industry-specific |
Policy transparency issues; no DPA for free tier |
|
Deployment |
Cloud-only, Meta-hosted |
On-premises, private cloud, hybrid options |
No self-hosted or air-gapped deployment |
Is WhatsApp safe?
Unfortunately, many WhatsApp users do not prioritize the security of the app, even though they trust it with not only data about their movements but also sensitive information such as bank cards and finances. Let’s begin by examining the security features and Security Certification that the developers claim are already integrated into the solution.
End-to-end encryption is one of the most important methods for ensuring user safety on WhatsApp. The main principle is to create a unique key that enables data decryption, with only the sender and recipient having access to it.

To check if end-to-end encryption is enabled, simply go to the chat section that corresponds to it. This method of ensuring user safety is highly effective because intercepted information cannot be identified by intruders. That is why most modern secure messengers precisely work on the basis of end-to-end encryption, utilizing the Signal protocol.
Another effective way to protect the privacy of interactions implemented in WhatsApp is two-factor authentication. This method involves the requirement of a confirmation code, which is sent to your personal mobile phone number, in order to access the account.
According to the developers, WhatsApp users’ conversations are not listened to or recorded, ensuring their privacy is guaranteed. Even the app’s system administrators do not have access to them, as they are also protected by end-to-end encryption.
This additional layer of security prevents unauthorized users from accessing your personal data, ensuring its protection. By combining this with the use of proxies, you further safeguard your online presence, making it even harder for unauthorized entities to infiltrate your accounts. You can rest assured knowing that no one will be able to use your account without your knowledge, because you will receive an immediate notification as soon as any activity is detected.
Key Insight #1: Encryption Scope Matters
End-to-end encryption protects messages in transit, but not necessarily at rest. WhatsApp’s cloud backups (iCloud/Google Drive) are not end-to-end encrypted by default, creating a critical vulnerability: intercepted backups or compromised cloud accounts expose entire chat histories.
Enterprise-grade solutions encrypt data both in transit and at rest, with keys managed by the organization—not a third-party platform.
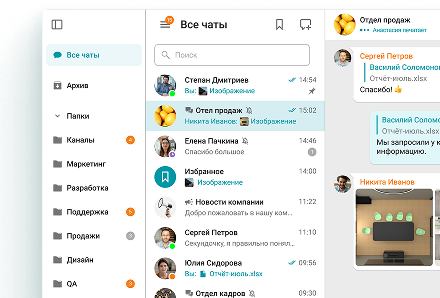
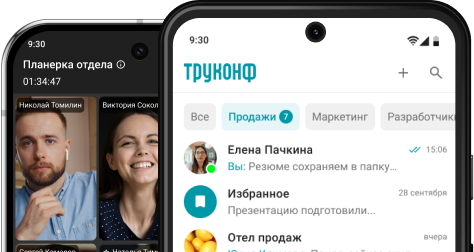
Your Messages Are Secure with TrueConf!
A powerful self-hosted video conferencing solution for up to 1,000 users, available on desktop, mobile, and room systems. Your confidential information is protected by 12 levels of security.
Most Common WhatsApp Security Issues
Despite all the methods of ensuring user protection and privacy, WhatsApp is not as secure as it initially appears. Not only has the application been at the center of multiple leak scandals, but some peculiarities of its functioning still remain dangerous.
Unencrypted Backups
As previously mentioned, WhatsApp utilizes end-to-end encryption during data transfer to protect your sensitive data and ensure secure communication. However, the information received on your device remains unprotected as it is stored in an unencrypted form.
There is a particular danger in the ability to create backups of chats, which is implemented on both Android and iOS. On the one hand, this feature can help users recover lost data if it was deleted.
However, you need to understand that, in this case, the information is stored in an unprotected form and can become the target of intruders. Your data may face additional risk if you use iCloud Backup or Google Drive to create a backup copy of your chats, alongside the local one.
Data Sharing
You may be surprised to find out that, despite the developers’ statements, WhatsApp collects a large amount of private data. The Privacy Policy of the application explains that the information is divided into three basic categories, including user-generated, automated, and third-party data.

The fact is, when communicating via WhatsApp, you automatically agree to provide not only information about your account. «Meta» has access to your phone number, as well as data on all the messages you send.
The company also receives information about your interests, hobbies, and field of activity from third-party applications and service providers that you use. Your bank cards and transactions are closely monitored, even if you have never discussed them with your interlocutor in chats, to help prevent identity theft.
As a result, «Meta» literally monitors your life constantly, and you have given the consent to this yourself. At the same time, it makes no sense to attempt to appeal to the current state of things with WhatsApp support.
Threat Landscape: What Could Go Wrong?
|
Threat Type |
Likelihood |
Potential Impact |
Mitigation in WhatsApp |
Residual Risk |
|---|---|---|---|---|
|
Cloud backup leak |
Medium-High |
Full chat history exposure |
Optional E2EE backup (user-enabled) |
High if not manually configured |
|
Phishing/social engineering |
High |
Account takeover, financial loss |
2FA, security notifications |
Medium (depends on user vigilance) |
|
Malicious desktop client |
Medium |
Device compromise, data theft |
App store verification only |
High for unofficial downloads |
|
Metadata profiling |
Certain |
Behavioral tracking, ad targeting |
None (core to Meta’s model) |
Very High |
|
Insider data exposure |
Medium |
Corporate data leakage |
No admin controls or remote wipe |
Very High for business use |
Cheating via WhatsApp
Due to the large number of WhatsApp users, it has become one of the most popular targets for cybercriminals. To ensure security, App Store and Google Play Store carefully regulate the client applications available, so that visitors’ personal data does not fall into the hands of hackers. Nevertheless, the situation is completely different with the WhatsApp desktop application, causing natural concerns.
The fact is that there have already been cases where attackers have disguised malicious software as an add-on for a legitimate solution, containing a Trojan virus. This method was used to both damage the computer and obtain personal data, such as bank card and passport numbers.
Phishing websites, which trick users into sharing personal information, are still a frequent method of fraud. Most often, unsuspecting people who enter their phone number for authorization are the victims of spam bombardment. Utilizing insider threat analytics and a robust threat hunting solution can help identify potential internal risks and prevent misuse of sensitive customer information.
Hacking of accounts with subsequent extortion is also a frequent case of user deception. The attackers portray loved ones who have encountered an emergency situation in order to force them to transfer a certain amount of money.
Key Insight #2: Governance Is a Security Feature
Consumer messengers like WhatsApp optimize for ease of use, not administrative control. In enterprise contexts, the inability to enforce password policies, remotely wipe corporate data from ex-employee devices, or generate audit logs for compliance reviews creates unacceptable risk.
Secure business platforms embed governance into their architecture—making compliance enforceable, not optional.
Tips for Making Communication Safer
There are several effective ways to make WhatsApp much safer than with regular use, regardless of whether you use WhatsApp for daily communication or for marketing purposes. However, these tools will only work if you take precautions and carefully monitor any suspicious activity, as well as the software:
- When creating an account, make sure to create complex passwords that include not only letters, but also numbers and symbols;
- Make sure to enable two-factor authentication to decrease the likelihood of your personal account being hacked;
- Do not give your phone number to users you do not know personally or whose authenticity you are unsure of;
- Make sure to include the security code on your mobile phone to prevent anyone from using it remotely;
- It is important to regularly update WhatsApp, as developers continually work to fix any detected problems, including those related to security;
- Regardless of the device you choose, it is important to use antivirus software to protect yourself from malware;
- For enhanced privacy of communication sessions, it is highly recommended to enable a VPN;
- Only use the web version of WhatsApp in a browser that does not have password and bank card storage enabled.
It is important to remind you that it is necessary to block any interlocutors who are attempting to obtain your personal data. Pay special attention to users whose behavior changes dramatically – it is highly likely that their account has been hacked.
Try TrueConf Server Free!
- 1,000 online users with the ability to chat and make one-on-one video calls.
- 10 PRO users with the ability to participate in group video conferences.
- One SIP/H.323/RTSP connection for interoperability with corporate PBX and SIP/H.323 endpoints.
- One guest connection to invite a non-authenticated user via link to your meetings.

WhatsApp and Business Communication
A corporate communications solution should not only support simultaneous connections for a large number of users but also ensure secure interactions and prevent identity theft. If WhatsApp can still handle the number of participants, then the security issue becomes highly controversial.
Let’s closely examine the possibility of utilizing this application for corporate purposes.
Compliance with GDPR Requirements
In 2016, the European Union adopted the General Data Protection Regulation (GDPR), which regulates the approach to electronic privacy. At the same time, the fundamental criteria of this legal act not only state the obligation of service providers to specify the personal information that will be collected, but also the purposes for which it will be used.
As mentioned earlier, WhatsApp has faced repeated accusations of not prioritising the security of personal data. Not only is the official list of collected information quite vague, but users also have no way to choose what exactly the solution can gather.
This policy applies equally to both the free version of the platform and WhatsApp for Business. In order to continue communicating on the platform, users of the application must agree to these terms. As a result, WhatsApp’s approach contradicts the security requirements necessary for ensuring safe corporate communication and compliance.
Lack of User Management
WhatsApp is not suitable for managing large enterprises as it has a maximum group capacity of only 100 users. Changing a mobile phone number can lead to problems: it is necessary to remove the participant from all chats to prevent a third party from accessing corporate information.
In the case of WhatsApp, it can be extremely difficult to immediately restrict access to confidential information if an employee leaves the company. The reality is that some information will remain on the employee’s smartphone, and the group administrator has no control over it.
Deployment Models: Why Architecture Affects Security
|
Deployment Type |
Control Level |
Data Residency |
Scalability |
Best For |
|---|---|---|---|---|
|
Consumer Cloud (WhatsApp) |
None (Meta-controlled) |
Global, undefined |
Limited to app constraints |
Personal use, informal teams |
|
Managed Business Cloud |
Partial (vendor SLAs) |
Region-selected options |
High, vendor-managed |
SMBs with moderate compliance needs |
|
On-Premises / Private Cloud (e.g., TrueConf) |
Full (organization-controlled) |
Fully defined, air-gap possible |
Enterprise-scale, customizable |
Regulated industries, government, security-first orgs |
Key Insight #3: The Hidden Cost of “Free”
WhatsApp’s zero monetary cost masks significant hidden expenses: compliance risk exposure, productivity loss from context-switching between personal/professional chats, and reputational damage from data incidents.
Enterprise platforms like TrueConf shift the model from “free but risky” to “investment-grade security,” where total cost of ownership includes risk mitigation, audit readiness, and operational continuity.
Mixing Work and Personal Life
WhatsApp remains one of the most popular apps for communicating with loved ones. However, adding business discussions to chats with family and friends can cause work to invade your personal life.
In such circumstances, it becomes virtually impossible to relax and distract oneself from professional affairs, as a rule. Many people who permanently combine work and home responsibilities often suffer from burnout for a long time.
Additionally, using a shared messenger can increase the likelihood of errors, which could potentially harm one’s reputation among colleagues. Sending a message to the wrong chat can jeopardize one’s career in some cases.
TrueConf: A Secure and Scalable Alternative to WhatsApp
TrueConf is a secure platform for corporate communication that offers a variety of features, including secure personal and group chats, video conferences, and tools for collaborating on tasks with teams. The solution is equipped with a multi-level security system that includes end-to-end encryption and operates within a closed network.
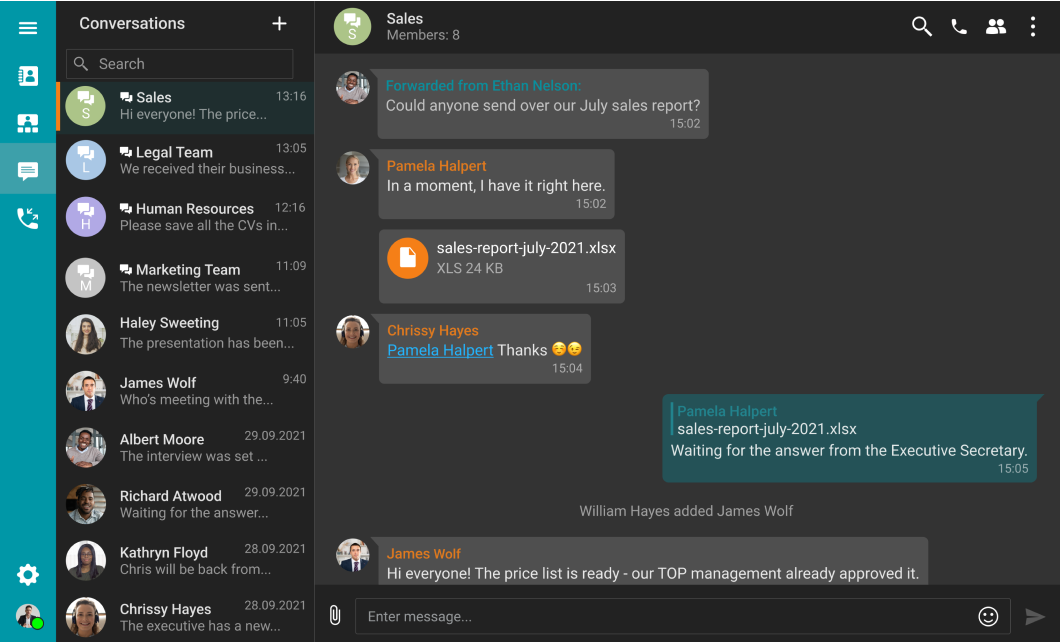
TrueConf fully complies with all GDPR requirements, ensuring secure and private interactions for companies of any size. The application works on almost all popular platforms, including iOS and Android, which means you can stay connected even during business trips.
Unlike consumer messengers, TrueConf gives organizations full control over data residency, user permissions, and security policies. Deploy on your own infrastructure or in a private cloud, enforce encryption standards, and maintain complete audit trails—without relying on third-party data processing.
FAQ
Is WhatsApp encrypted enough for business use?
WhatsApp uses end-to-end encryption for messages in transit, which is strong for personal use. However, business environments often require encryption at rest, centralized key management, and audit capabilities—features that TrueConf provides natively to meet enterprise security standards.
Can I prevent WhatsApp from sharing my data with Meta?
WhatsApp’s privacy policy requires consent to data collection for service operation and improvement, with limited opt-out options. For organizations needing strict data isolation, TrueConf operates in closed networks with no third-party data sharing, giving you full sovereignty over communications.
What if I need to revoke access when an employee leaves?
WhatsApp offers no admin tools to remotely wipe corporate data from personal devices or deactivate accounts centrally. TrueConf includes enterprise identity integration and administrative controls to instantly revoke access and enforce data retention policies across all endpoints.
Does WhatsApp support compliance frameworks like GDPR or HIPAA?
WhatsApp provides limited GDPR documentation but lacks features like data processing agreements for the free tier, audit logs, or data residency guarantees required for regulated industries. TrueConf is designed with compliance-by-design architecture, supporting GDPR, HIPAA, and sector-specific mandates out of the box.
Can I use WhatsApp securely if I enable all privacy settings?
Enabling two-factor authentication and encrypted backups improves personal security, but fundamental limitations remain: Meta still processes metadata, backups rely on third-party cloud security, and there’s no administrative oversight. TrueConf eliminates these structural risks by placing control entirely in your organization’s hands.
Is there a way to keep work and personal chats separate on WhatsApp?
WhatsApp Business offers a separate app, but both versions share the same underlying infrastructure and data policies with Meta. TrueConf provides a dedicated, isolated environment for professional communication, preventing accidental data leakage and reducing burnout from context switching.
How does TrueConf handle encryption compared to WhatsApp?
Both use end-to-end encryption for messages in transit, but TrueConf extends protection to data at rest, supports organization-managed encryption keys, and allows deployment in air-gapped environments. This layered approach ensures security aligns with enterprise risk tolerance, not just consumer convenience.
About the Author
Nikita Dymenko is a technology writer and business development professional with more than six years of experience in the unified communications industry. Drawing on his background in product management, strategic growth, and business development at TrueConf, Nikita creates insightful articles and reviews about video conferencing platforms, collaboration tools, and enterprise messaging solutions.








Follow us on social networks