Is Zoom Secure? Privacy Risks, Security Issues & Safer Alternatives (2026 Update)
Updated March 2026
Quick Verdict: Is Zoom Secure in 2026?
Zoom is significantly more secure than it was in 2020, but “more secure” does not mean “secure by default.” The honest answer depends on three variables: your plan tier, your configuration, and your risk tolerance.
|
Use Case |
Risk Level |
Recommended Action |
|---|---|---|
|
Casual personal calls |
🟢 Low |
Default settings are fine |
|
Small business meetings |
🟡 Medium |
Enable waiting rooms + passcodes |
|
Healthcare / legal / finance |
🟠 High |
Require E2EE + BAA + paid plan |
|
Government / classified data |
🔴 Very High |
Do not use Zoom; use air-gapped or on-premises platform |
The 60-Second Summary
Encryption: AES-256 GCM is on by default, but it is in-transit encryption — Zoom’s servers hold the keys. True end-to-end encryption (E2EE) must be manually enabled and disables cloud recording, live transcription, and breakout rooms.
Track record: 30 CVEs were published for Zoom products in 2025, down from 36 in 2024. One critical flaw (CVE-2025-49457, CVSS 9.6) was patched in August 2025.
Compliance: SOC 2 Type II, ISO 27001, HIPAA-ready (paid plans + BAA), FedRAMP Moderate (Zoom for Government only), GDPR with DPAs available.
Persistent risks: Misconfigured meetings, third-party integrations with separate privacy policies, and AI Companion data processing if not opted out.
Zoom’s Data Collection and Privacy Practices
What Personal Data Does Zoom Collect?
Zoom gathers various categories of user-related details to operate and maintain its functionality. This covers fundamental information like full names, registered emails, contact numbers, and hardware specifications. Moreover, Zoom monitors supplementary metadata concerning sessions, which can involve IP origins, hardware signatures, and time stamps for meetings. It may also store information tied to meeting contents, such as written chats and uploaded materials, though such content is generally preserved briefly for processing purposes.
As of Zoom’s January 2026 privacy policy update, the platform explicitly states it does not sell personal data to third parties. However, meeting audio, video, and chat content can be used for AI model training unless an account admin actively opts out — a distinction that matters for enterprise buyers.
Zoom has received criticism regarding the way it distributes user-related records with external partner companies. Reports revealed that the platform previously transmitted certain analytics information to entities like Facebook along with advertising collaborators. For example, the iOS application from Zoom once delivered user session statistics to Facebook without securing explicit permission, sparking data protection debates. While the company has later updated policies to mitigate these challenges, the exchange of personal records remains an ongoing concern for participants.
Data Mining and Privacy Concerns
Zoom’s background data-gathering functions have likewise drawn scrutiny, particularly because of a capability that accessed LinkedIn profile information. This mechanism unintentionally revealed sensitive details about individuals without them granting direct approval. You can use a digital footprint checker to see what personal information of yours is already publicly accessible, including details shared without your knowledge or consent. These cases highlight why it is crucial to thoroughly examine the specific clauses within a service’s privacy terms to properly grasp how user information might be obtained and applied.
Zoom Security Vulnerabilities
Lack of End-to-End Encryption
A major protection issue surrounding Zoom is the lack of default end-to-end encryption. Although this option exists, it is not switched on automatically. As a result, in numerous cases, Zoom calls are only partially encrypted, which could leave them exposed to interception or unwanted entry. This represents a serious issue for participants dealing with private or sensitive content during online conferences.
Unique Insight #1
Zoom’s default in-transit encryption uses a server-side key model where Zoom infrastructure manages decryption — meaning that a sufficiently privileged insider, a subpoena, or a server-side breach could theoretically expose meeting content.
By contrast, when E2EE is enabled, the decryption keys never leave participant devices, so even a full breach of Zoom’s cloud infrastructure would yield only ciphertext.
Key takeaway: Organizations handling legally privileged or regulated communications — including attorneys, physicians, and financial advisors — should treat E2EE as non-negotiable, not optional.
Zoom Meeting ID Vulnerability
Zoom meeting identifiers may be easily created by attackers through widely accessible software. This flaw permits unauthorized participants to access meetings without an official invite, disrupting conversations and risking exposure of confidential material. Hosts should apply additional safeguards such as passwords and waiting-room controls to block these types of incidents.
CVE-2025-49457: The Critical Windows Flaw You Need to Know About
In August 2025, Zoom’s own internal Offensive Security team discovered and disclosed CVE-2025-49457, a critical untrusted search path vulnerability affecting Zoom Clients for Windows. The flaw scored 9.6 out of 10 on the CVSS severity scale. It exploits how Zoom loads dynamic-link libraries (DLLs): because the application does not specify absolute file paths, an attacker can place a malicious DLL on an accessible network share. When Zoom loads that library, the attacker’s code executes with Zoom’s privileges — without requiring any authentication.
Affected products included Zoom Workplace Desktop, Rooms, Rooms Controller, VDI Client, and Meeting SDK for Windows, all versions prior to 6.3.10. Zoom released a patch in version 6.3.0. If your organization has not updated Zoom for Windows past version 6.3.10, you remain exposed. This is the second DLL-hijacking class vulnerability patched in the Windows client (following CVE-2024-24697 in 2024), suggesting a systemic pattern worth monitoring.
Public Exposure of Zoom Calls
There have been occasions when individual or corporate Zoom meetings were mistakenly made publicly visible across the web. Such situations can arise from incorrect configuration settings or flaws inside Zoom’s cloud-based storage systems. These cases stress the dangers of hosting private calls on a service that stores them remotely without strict protective measures.
Cloud Recording Risks
Zoom’s recording-to-cloud capability, while convenient for documentation purposes, also introduces security concerns. These stored files reside on Zoom-managed servers, which could be subject to breaches unless locked down effectively. Past incidents have shown meeting footage being shared with unintended audiences, illustrating the inherent danger of relying entirely on online storage for critical communications.
Security Concerns During Meetings
One of the most well-known Zoom security problems is “zoombombing,” where uninvited individuals enter a meeting and cause interference. Such disruptions can vary from harmless pranks to major confidentiality violations, especially if private data is discussed. Cyber-intruders may quickly join calls if organizers neglect to enforce passwords or omit waiting-room controls for entry management.
Zoom Adds Strangers to Public Contact Lists
Zoom’s automated mechanism for placing unfamiliar users into shared contact lists has prompted warnings about the potential exposure of personal emails and profile visuals. This weakness endangers user privacy by granting strangers visibility into details outside the intended communication circle.
Hackers Posting Zoom Accounts on the Dark Web
Beyond vulnerabilities in the service itself, reports have surfaced about Zoom login information being traded on the dark-web marketplace. This suggests criminals could log into accounts if those credentials were compromised elsewhere. Strong, distinct passwords and enabling two-factor verification are essential measures to guard against this threat.
Unique Insight #2
Zoom’s SSO enforcement feature (available on Business and Enterprise plans) eliminates password-based credential risk by delegating authentication entirely to the organization’s identity provider (e.g., Okta, Azure AD, Google Workspace). When SSO is enforced, employees cannot create personal Zoom passwords that could be reused or phished. Organizations that enforce SSO + MFA reduce their Zoom account takeover risk to near zero for credential-stuffing attacks — the leading cause of Zoom credential leaks reported on dark web forums.
Addressing Zoom’s Security and Privacy Issues
Updates and Fixes to Security Flaws
Zoom has taken meaningful actions to resolve security and privacy issues flagged by the community and cybersecurity professionals. The service rolled out stronger encryption methods, expanded authentication tools, and improved granular meeting-management settings.
Zoom’s 2025 CVE count of 30 (average base score 6.3/10) represents a measurable improvement over 36 CVEs in 2024. The company maintains a bug bounty program and publishes regular security advisories at its Trust Center.
Although these revisions have boosted Zoom’s security reputation, participants must continue staying alert and use the newest protective functions.
Compliance Certifications (2026 Status)
Zoom holds the following certifications relevant to enterprise and regulated-industry buyers:
|
Standard |
Status |
Notes |
|---|---|---|
|
SOC 2 Type II |
✅ Active |
Verified by independent auditor on sustained basis |
|
ISO 27001 |
✅ Active |
International standard for information security management |
|
HIPAA |
✅ Paid plans + BAA required |
Free tier does not qualify |
|
FedRAMP Moderate |
✅ Zoom for Government only |
Separate infrastructure from consumer Zoom |
|
GDPR |
✅ DPA available |
EU data residency option; SCCs for international transfers |
|
FERPA/COPPA |
✅ Zoom for Education accounts |
Must use dedicated education account type |
8 Security Settings to Configure Right Now
Zoom’s default settings are reasonable but not sufficient for sensitive use. These changes take under five minutes and close the most common attack vectors:
- Require meeting passcodes. Settings > Security: enable “Require a passcode when scheduling new meetings.” Verify it has not been toggled off.
- Enable the Waiting Room. Waiting Room is the single most effective barrier against uninvited guests. Every participant waits for host approval before entering.
- Lock the meeting after everyone joins. Click Security in the toolbar → “Lock Meeting.” No one else can join even with the correct link and passcode.
- Disable file transfer in chat. Settings > In Meeting (Basic): toggle off “File transfer.” Prevents participants from distributing malware via Zoom chat.
- Restrict screen sharing to host. Set “Who can share?” to “Host Only.” Grant sharing permission individually during the call as needed.
- Enable E2EE for confidential meetings. Settings > Security: toggle on E2EE, then select it per meeting. Accept the trade-off: no cloud recording or live transcription.
- Disable join before host. Settings > In Meeting (Advanced): toggle off “Allow participants to join before host.” Prevents unsupervised conversations in your meeting room.
- Enforce authenticated profiles. Settings > Security: enable “Only authenticated users can join meetings.” This requires participants to have a Zoom account, eliminating fully anonymous access.
How to Identify the Shield Icon in the Meeting Window?
Zoom includes a shield symbol inside the meeting display to signal that the connection is protected. Participants should always check for this mark before starting private discussions to confirm that the session is secure.
Should You Still Use Zoom?
Even with some remaining security gaps, Zoom is still a heavily used and easy-to-navigate video conference application, and for most everyday business use it is secure enough. The honest assessment: Zoom’s 2020 security failures were real, but the company has addressed the most critical structural issues. The platform now holds enterprise-grade compliance certifications, patches vulnerabilities faster than most comparable vendors, and provides granular controls for administrators.
The remaining risks are primarily configuration risks, not architectural ones. Zoombombing, credential theft, and data exposure are largely preventable with the eight settings above. The one genuine architectural limitation — the lack of E2EE by default — is a known trade-off that Zoom has made transparent, and it can be overridden for sensitive meetings at the cost of some collaboration features.
Unique Insight #3
Zoom’s free plan does not qualify for a HIPAA Business Associate Agreement (BAA), which means healthcare providers who use free accounts for patient consultations are technically operating outside HIPAA compliance — regardless of any other settings they configure. The BAA is available only from the Business tier upward. Healthcare organizations, therapists, and any provider handling Protected Health Information (PHI) must confirm their Zoom subscription level before the first telehealth session; using a free or Pro account exposes the organization to HIPAA enforcement action even if the session itself was never breached.
Zoom Alternatives
If considering a transition from Zoom or exploring other options, here are several alternatives that provide secure and comprehensive features tailored for different business requirements:
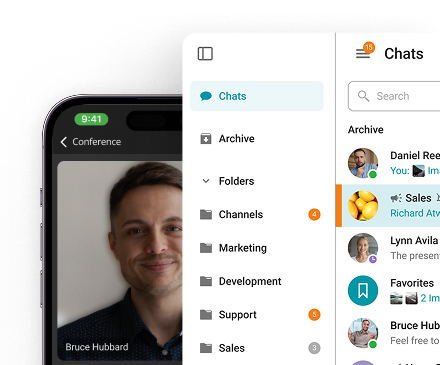
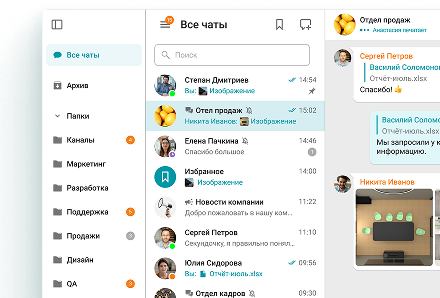
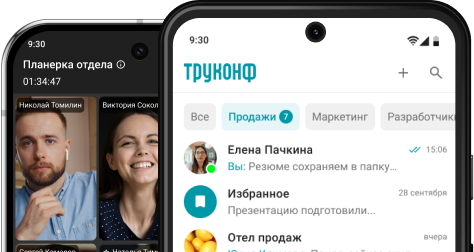
TrueConf
TrueConf is a secure video conferencing solution designed for both small businesses and large organizations. It offers encryption, safeguarding the confidentiality and security of all meetings and communications. The solution provides flexible deployment options, including on-premises and cloud solutions, ensuring it can meet the specific requirements of any business.
With high-definition video and clear audio, TrueConf ensures a seamless meeting experience, even for large events. The platform’s integration with various IT systems allows businesses to connect TrueConf with existing software, such as Active Directory, and other collaborative solutions. The solution is a reliable option for organizations that prioritize both security and adaptability in their communication tools.
Try TrueConf Server Free!
- 1,000 online users with the ability to chats and mske one-on-one video calls.
- 10 PRO users with the ability to participate in group video conferences.
- One SIP/H.323/RTSP connection for interoperability with corporate PBX and SIP/H.323 endpoints.
- One guest connection to invite a non-authenticated user via link to your meetings.

Google Meet
Google Meet delivers end-to-end encryption to secure all sessions. It integrates seamlessly with Google Workspace, making scheduling, hosting, and collaborating a straightforward process within one ecosystem. Close ties with Google Calendar enhance convenience for organizations already using Google’s productivity products.
Microsoft Teams
Microsoft Teams combines conferencing with shared workspaces, file-sharing, and instant messaging. It features advanced security like multi-factor authentication and E2EE for 1-on-1 calls. Deep integration with Microsoft 365 makes it a natural fit for companies committed to Microsoft tools, and it supports customization for webinars and app integrations.
Cisco Webex
Cisco Webex is a long-standing enterprise communication solution known for its privacy and reliability. It offers complete encryption, password-protected sessions, and the ability to lock rooms to block intruders. In addition to video calls, Webex facilitates document exchange, teamwork, and virtual events, catering especially to large organizations needing scalability and compliance.
These options offer diverse features that serve businesses of various sizes, with robust security, integrations, and personalization. Whether an organization prefers a simple platform like Google Meet or an enterprise-level choice like Microsoft Teams, there are secure tools to meet the need.
Conclusion: Is Zoom Safe?
Zoom can be regarded as safe enough for daily communications, though certain privacy and safety risks still exist. While the company has made notable progress in addressing earlier flaws, it remains crucial for individuals to apply protective settings. Those desiring maximum privacy may either leverage Zoom’s enhanced functions or adopt services that prioritize encryption and confidentiality by default.
Empower your video conferencing security with TrueConf!
Is Zoom end-to-end encrypted by default? No. Zoom uses AES-256 GCM in-transit encryption by default, meaning Zoom’s servers hold the decryption keys and could theoretically access meeting content. True E2EE is available but must be enabled manually by the host. Enabling it disables cloud recording, live transcription, and breakout rooms. Has Zoom been hacked or breached? Zoom experienced several serious security incidents in 2020, including data routing through Chinese servers, unauthorized Facebook data sharing, and mass Zoombombing. An $85 million class-action settlement followed. Since then, no large-scale data breach has been publicly confirmed, though Zoom continues to patch vulnerabilities regularly — including CVE-2025-49457, a critical Windows privilege-escalation flaw patched in August 2025. Is Zoom safe for healthcare and HIPAA compliance? Yes, but only on paid plans (Business tier and above) with a signed Business Associate Agreement (BAA) in place. The free tier does not qualify for a BAA. Healthcare providers must also enable E2EE, disable cloud recording by default, and use waiting rooms. Using a free or Pro account for Protected Health Information (PHI) constitutes a HIPAA compliance risk regardless of other settings. What is Zoombombing and is it still a risk in 2026? Zoombombing refers to uninvited users crashing Zoom meetings, often with offensive content. It became epidemic in 2020 because meetings had no passwords or waiting rooms by default. Zoom has since made passwords and waiting rooms on by default for new meetings, substantially reducing this risk. The threat persists only in older accounts where default settings were never updated, or where admins have explicitly disabled these protections. What is the most secure alternative to Zoom for enterprises? For maximum data sovereignty, an on-premises platform such as TrueConf Server is the strongest option — all communication stays inside the organization’s own network, with no data passing through third-party cloud infrastructure. For organizations requiring a cloud solution with strong compliance credentials, Cisco Webex (HIPAA, FedRAMP) or Microsoft Teams (integrated with Azure AD and Microsoft Defender) are the closest enterprise-grade alternatives.FAQ
About the Author
Olga Afonina is a technology writer and industry expert specializing in video conferencing solutions and collaboration software. At TrueConf, she focuses on exploring the latest trends in collaboration technologies and providing businesses with practical insights into effective workplace communication. Drawing on her background in content development and industry research, Olga writes articles and reviews that help readers better understand the benefits of enterprise-grade communication.








Follow us on social networks