What is Cybersecurity? Definition, Importance & Key Concepts
Updated April 2026
Executive Summary
Cybersecurity is the practice of protecting computers, servers, networks, and data from digital attacks, unauthorized access, and damage. For modern businesses—especially those relying on video conferencing, collaboration platforms, and hybrid work infrastructure—cybersecurity is not optional; it is foundational to operational continuity, regulatory compliance, and customer trust.
This guide explains core cybersecurity concepts, threat categories, and practical defense strategies. It also highlights how enterprise communication platforms like TrueConf integrate security-by-design principles to support secure, compliant, and resilient digital collaboration.
|
Key Area |
Core Insight |
Practical Takeaway |
|---|---|---|
|
Definition |
Cybersecurity protects digital assets through people, processes, and technology |
Security must be layered, proactive, and continuously updated |
|
Top Threats |
Malware, phishing, ransomware, identity theft, and cloud misconfigurations dominate |
Employee training + technical controls = strongest defense |
|
Deployment Models |
On-premises, cloud, and hybrid each have distinct security implications |
Choose architecture based on data sensitivity, compliance needs, and control requirements |
|
Human Factor |
Users are both the first line of defense and the most common attack vector |
Regular security awareness training is non-negotiable |
|
TrueConf Relevance |
Secure video conferencing requires encryption, access control, and auditability |
Platforms with on-premises deployment options reduce exposure to external threats |
What is Cybersecurity?
Cyber protection, often referred to as IT security, involves safeguarding computers, data servers, portable devices, electronic infrastructures, network systems, and confidential information from digital intrusions or illegal access. This forms an essential part of tech management, which includes anticipating, identifying, and countering cyber risks. These risks can take a variety of forms, such as deceptive phishing, harmful malware, data hijacking ransomware, and disruptive denial of service attacks. Cybersecurity strategies are implemented to preserve the integrity, secrecy, and accessibility of data, making sure that digital systems are functioning at peak capacity. The importance of this sector has grown exponentially as an increasing number of corporations and private individuals store critical information on digital mediums, thus becoming potential victims for cybercriminals.
Human Factor
Considering the realm of cybersecurity, human beings represent the most vital element. This encompasses individuals ranging from IT specialists responsible for maintaining and securing network infrastructures, to each individual who logs into these systems. Usually, humans serve as the initial barrier in cybersecurity. It is imperative for IT experts to keep themselves updated about novel risks and safety measures, while end-users need to understand potential threats and methods of circumventing them. This awareness often begins with a solid grasp of network security fundamentals, providing the necessary context to recognize how individual actions impact the broader digital environment. This might involve steps like refraining from opening dubious emails or making sure that information is frequently backed up.
Nevertheless, the human factor can also pose the greatest vulnerability in cybersecurity. Errors committed by humans, such as succumbing to phishing tricks or utilizing weak credentials, can result in substantial security infringements. This emphasizes the necessity for continuous learning and instruction in cybersecurity best practices for everyone employed within a company.
Furthermore, humans aren’t solely participants in the defensive side of cybersecurity. They also take on roles as offenders, like hackers attempting to penetrate systems for nefarious reasons. Comprehending the motives and tactics of these individuals can be pivotal in formulating effective cybersecurity plans. This understanding of both offensive and defensive perspectives has led to collaborative approaches in cybersecurity testing, such as implementing a purple team in cybersecurity that combines red team attack simulations with blue team defensive strategies to create more comprehensive security assessments.
Insight #1: The Control Paradox
Many organizations over-invest in technical controls while under-investing in user empowerment.
The most resilient security posture balances automation with human judgment—training staff not just to follow rules, but to recognize context.
Platforms that simplify secure behavior (like one-click encrypted meetings in TrueConf) reduce the cognitive load on users and lower the risk of security fatigue.
To sum up, humans are crucial to both the robustness and susceptibility of cybersecurity. Their actions and conduct can significantly impact the security of data and systems, highlighting the requirement for thorough and continuous Cybersecurity Certification Training and consciousness.
Processes
In the realm of cybersecurity, “processes” signify the assortment of methods and rules that companies adopt to safeguard their digital systems from prospective security threats. These might encompass measures to pinpoint weak spots, initiatives to obstruct unauthorized entry, and contingency plans for the instance a security violation transpires. Procedures also include periodic checks and modifications to make sure the security protocols remain potent against emerging cyber threats, often using vulnerability scanners to identify weaknesses before they can be exploited. In addition to these procedures, many organizations implement a fraud management system to detect and mitigate fraudulent behavior across digital channels. These systems work in tandem with cybersecurity protocols to monitor transactions, flag anomalies, and respond to suspicious activity in real time—thereby reinforcing the broader defense mechanisms against cybercrime. These are a critical component of a holistic cybersecurity approach, as even the most sophisticated security tech can become ineffectual if the procedures governing its application are deficient or faulty. It is equally crucial that these procedures are transparently conveyed and comprehended by every member of the corporation since human miscalculation can frequently be a vulnerability in cybersecurity fortifications.
Technology
Within the realm of cybersecurity, advanced technology serves as an essential instrument in shielding crucial data and systems from significant cyber risks. Cybersecurity technology is specifically engineered to thwart, identify, and alleviate cyber-attacks. It encompasses an extensive assortment of systems including network firewalls, WAFs, intrusion prevention systems, anti-malware software, cryptographic tools, among others. This technology encompasses an extensive assortment of systems including firewalls, intrusion prevention systems, anti-malware software, cryptographic tools, among others. Alongside these systems, dast software plays an important role by scanning and testing web applications in real time to detect potential security flaws by simulating external attacks to uncover vulnerabilities. These cutting-edge technologies are utilized to ensure the preservation of data integrity, secrecy, and accessibility. They assist in safeguarding networks and devices from unauthorized intrusion, data leaks, and additional cyber risks. Incorporating cyber threat intelligence into these systems enhances their ability to anticipate and respond to emerging threats with greater precision and speed.
As technology progresses, the parameters of cybersecurity also broaden. The emergence of artificial intelligence, machine learning, and distributed ledger technologies have ushered in novel aspects to cybersecurity. These advanced technologies are employed to augment the functionality of cybersecurity tools, thereby making them more potent and streamlined. However, these technologies also pose new hurdles and weak points that necessitate attention. As such, keeping abreast of the most recent trends, AI security practices, and technological progress is vital within the cybersecurity sphere.
In summary, technology can be viewed as both a blessing and a curse in relation to cybersecurity. Even though it provides sophisticated tools and strategies to shield digital assets, it simultaneously presents new susceptibilities and threats. Consequently, the objective of cybersecurity is to utilize technology effectively to guarantee optimal security while minimizing potential hazards. For organizations looking to manage digital assets securely and efficiently, consulting a DAM system buyers guide can help select the right platform, ensuring that new technologies are leveraged safely while protecting valuable content.
Common Cybersecurity Risks for Companies
|
Risk Category |
Typical Impact |
High-Risk Industries |
|---|---|---|
|
Phishing & Social Engineering |
Credential theft, data exfiltration, ransomware deployment |
Finance, Healthcare, Legal |
|
Ransomware |
Operational downtime, financial loss, reputational damage |
Education, Government, Manufacturing |
|
Insider Threats |
Data leakage, policy violations, accidental exposure |
Tech, Consulting, Remote-First Orgs |
|
Cloud Misconfiguration |
Unauthorized data access, compliance violations |
SaaS Providers, Startups, E-commerce |
|
Unsecured Endpoints |
Device compromise, lateral movement in networks |
Hybrid Workforces, Field Services |
Insight #2: The Deployment Model Decision Is a Security Decision
Choosing between cloud, on-premises, or hybrid deployment isn’t just about cost or scalability—it directly shapes your threat surface.
On-premises solutions like TrueConf Server keep video traffic and meeting data within your corporate firewall, eliminating exposure to third-party cloud breaches.
This architectural choice is especially critical for regulated sectors where data residency and auditability are non-negotiable.
Types of Cybersecurity Solutions
Cybersecurity is not a single product but a layered ecosystem of complementary controls. Below is a functional taxonomy of solution categories:
- Preventive Controls – Firewalls, endpoint protection, email filtering, and access management stop threats before they execute.
- Detective Controls – SIEM systems, intrusion detection, and behavioral analytics identify anomalies in real time.
- Corrective Controls – Backup/recovery tools, incident response playbooks, and patch management restore operations post-incident.
- Governance & Compliance – Policy engines, audit logs, and compliance frameworks (e.g., ISO 27001, NIST) ensure accountability.
Businesses these days are turning to different cybersecurity solutions for protecting sensitive data. This also helps them comply with the Digital Personal Data Protection Act I think. Network security tools prevent unauthorized access and cyberattacks while endpoint security protects devices such as laptops and mobile phones. Cloud solutions make sure online data stays safe through encryption and monitoring. I am controls user permissions to lower the chance of data breaches. Backup and recovery options help restore information after cyber problems occur. These measures do improve data protection and customer trust.
For communication platforms, security must be embedded at every layer: transport encryption (TLS/SRTP), user authentication (SSO/MFA), data residency controls, and administrative audit trails.
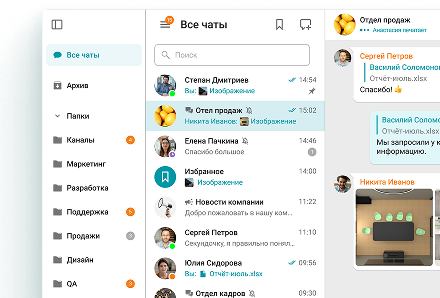
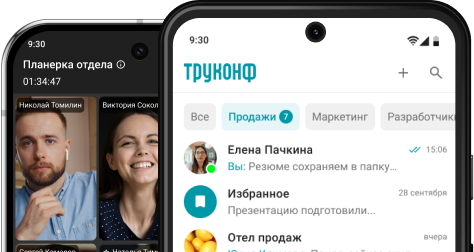
TrueConf exemplifies this approach by offering on-premises deployment, end-to-end encryption options, and granular role-based access—enabling enterprises to meet strict security policies without sacrificing collaboration capabilities.
Types of Cybersecurity Threats
Various forms of cybersecurity threats exist, each posing distinct challenges for individuals or businesses. One common category encompasses malware, encompassing harmful software such as viruses, worms, Trojans, ransomware, and spyware. These dangerous applications can compromise, encrypt, or erase sensitive information, manipulate critical computer functions, and track computer usage without the user’s knowledge.
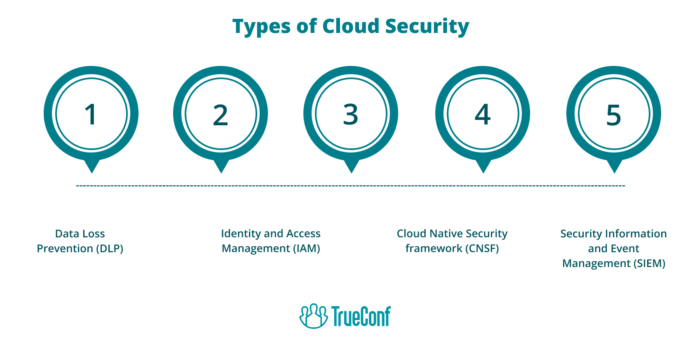
Cloud Security
Falling under the extensive array of cybersecurity dangers, Cloud Security emerges as an important class that requires particular consideration. As an increasing number of companies rapidly transition their functions and data repositories to cloud based services systems, the safety of these systems has escalated to become a critical worry. Cloud security is defined by the guidelines, checks, methods, and technological systems used to safeguard data, software, and the infrastructure connected with cloud computing.
The hazard environment in cloud protection is immense and constantly adapting. Some prevalent risks encompass data infiltrations, data disappearance, account commandeering, threats from within, insecure APIS, and denial of service onslaughts. These dangers can culminate in significant financial deficits, harm to brand image, and erosion of client confidence.
Financial and transactional security is a key part of this. Businesses handling payments —such as those using platforms like ZPay,must prevent fraud and disputes, and specialized tools, such as this list of chargeback software from SEON, help monitor, manage, and resolve these challenges efficiently, safeguarding transactions and maintaining customer confidence. For businesses exploring custom fintech solutions, security is a key feature they must implement. Any early-stage fintech firms apply for AWS credits through programs like AWS Activate to offset the costs of these high-security environments, allowing them to leverage premium fraud-prevention infrastructure without draining their initial capital.
Consequently, the enactment of sturdy cloud security protocols and data protection services is vital in preserving the wholeness and confidentiality of classified data and averting unauthorised entry or leakage. Organizations leveraging AWS cloud engineering services often benefit from built-in security frameworks and scalable tools that simplify the implementation of robust cloud protection strategies. Professionals in the cybersecurity field frequently utilise a range of instruments and tactics like encryption, access regulation, intrusion alert systems, and security assessment to ensure thorough cloud security.
Identity
The term ‘Identity’ denotes a distinct class of cybersecurity hazards in which digital criminals manipulate the digital persona of individuals or companies. This particular cybersecurity danger frequently employs malicious strategies like phishing, identity thievery, or spoofing. The primary objective remains to trick users into divulging confidential data, enabling the intruder to imitate the victim and secure unauthorized entry to systems and information. As a preventive measure, individuals can use tools that offer a credit lock feature to restrict unauthorized access to their financial identity and reduce the risk of fraud. Digital criminals have the ability to use purloined identities to execute fraud, execute transactions, disseminate malware, or even initiate targeted assaults against different organizations. The risk to identity highlights the necessity of applying strong authentication and access management protocols in cybersecurity, as well as improving identity visibility to monitor and control who has access to sensitive systems and data.
Malware
Malicious software, also known as malware, represents a significant cybersecurity risk that includes various detrimental software types like viruses, worms, Trojan horses, ransomware, spyware, and adware. Such malicious software can penetrate and harm devices, pilfer confidential data, and interrupt operations. The distribution of malware typically occurs through email attachments, software downloads, system vulnerabilities, or by visiting compromised websites.
A prevalent form of malware, viruses have the ability to self-replicate and disperse to other files or systems, often leading to widespread damage. Worms bear similarities to viruses but possess the ability to propagate independently, eliminating the need for a host program. Trojan horses present themselves as genuine software but can grant cybercriminals remote access to a device once they’re installed.
Ransomware represents a particularly menacing type of malware that locks a user’s files, demanding a ransom for the restoration of access. Spyware stealthily collects a user’s data without their consent, frequently used for marketing purposes. Lastly, although adware is less damaging, it can be invasive and expose users to additional cybersecurity risks.
The most effective defense against malware involves the use of up-to-date antivirus software, the adoption of secure browsing habits, avoiding the opening of email attachments received from unfamiliar sources, and seeking professional virus removal when needed. Regularly backing up critical data can also lessen the impact of a malware attack.
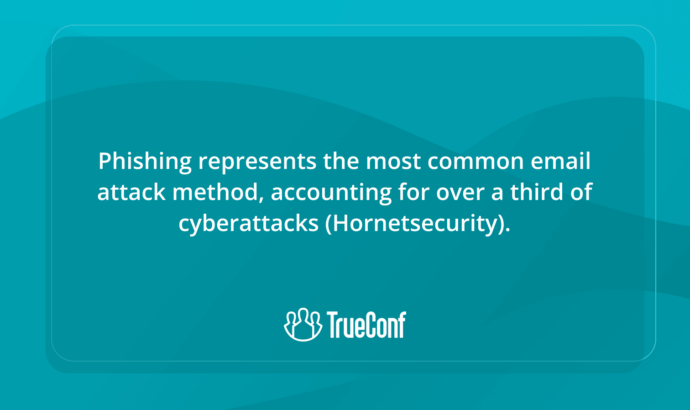
Phishing
Phishing represents a widespread and subtle form of cyber threat. This typically involves employing misleading emails, sites, or text messages to dupe people into disclosing confidential data like passwords, credit card details, or Social Security digits. The culprits disguise themselves as a reliable figure, often mimicking reputable organizations or individuals to gain the unsuspecting victim’s confidence. There exist various forms of phishing attacks, such as spear phishing, where distinct individuals or firms are specifically targeted; and whaling, where top-tier executives become the primary targets. Phishing can lead to substantial financial damages and data leaks, thereby posing a serious risk to both individual users and corporate entities. Therefore, cybersecurity strategies should incorporate strong safeguards against phishing assaults, along with continuous education to assist users in identifying and sidestepping such hazards.
Ransomware
Ransomware remains one of the most commonly seen cybersecurity threats. This particular type of malicious software has been designed specifically to restrict the user’s access to a computer system, unless a certain amount of money, also known as a ‘ransom’, is handed over. Both individual users and large-scale businesses or organizations can become the target of ransomware attacks. The cybercriminal usually gains access to the system via a cleverly disguised phishing scam, which tricks the unsuspecting user into clicking a link that appears harmless, but in reality, downloads the ransomware. Such type of scam is happening on PayPal nowadays. Once the malicious software has infiltrated a system, it commences the encryption of files and folders, rendering them useless to the user. Following the encryption, a message pops up demanding a certain payment in order to decrypt and regain access to the blocked files. This payment is typically demanded in a digital currency, such as Bitcoin, in an attempt to maintain the attacker’s anonymity. Fortunately, some systems and services provide flexible payment options, making it easier for victims to respond without adding unnecessary complications. The existence of ransomware presents a severe risk to cybersecurity, as it can result in substantial financial loss and service disruption. Therefore, it is crucial for both individuals and organizations to regularly back up their data and implement stringent security procedures to defend against potential ransomware attacks.
Zero Trust
One particular cybersecurity threat that corporations often confront is the absence of a stringent non-trust policy. The non-trust strategy is a specific safety principle demanding every user, even those within the corporation’s intranet, to undergo authentication, authorization, and ongoing verification of security setup and stance, prior to gaining or retaining access to software and information. This methodology minimizes the risk of an internal threat, a situation that arises when employees inside the corporation misuse their granted access to deliberately or inadvertently breach security. Moreover, it safeguards against outside threats by restricting network access and consistently checking security protocols. In the absence of a non-trust policy, a corporation’s intranet becomes vulnerable to a multitude of cyber threats, such as data leaks and assaults on network assets. Many organizations now adopt specialized zero trust security services in USA to strengthen this model and ensure compliance with modern cybersecurity standards. In the absence of a non-trust policy.
Cybersecurity Frameworks and Compliance
Organizations do not build security from scratch—they align with established frameworks that provide structure, benchmarks, and auditability.
Key frameworks include:
- NIST Cybersecurity Framework (CSF) – Widely adopted in the U.S.; focuses on Identify, Protect, Detect, Respond, Recover.
- ISO/IEC 27001 – International standard for information security management systems (ISMS).
- GDPR – EU regulation mandating data protection and breach notification for personal data.
- HIPAA – U.S. healthcare standard for protecting patient health information.
- SOC 2 – Trust services criteria for security, availability, processing integrity, confidentiality, and privacy.
Organizations working toward SOC 2 alignment often rely on specialized soc 2 compliance tools to streamline evidence collection, monitor security controls, and maintain continuous compliance across cloud and hybrid environments. These tools help reduce manual audit overhead while improving visibility into security posture and operational risk. Compliance is not a one-time checkbox but an ongoing discipline. Platforms that support compliance out of the box—through features like audit logs, data residency controls, and role-based permissions—reduce the operational burden on security teams.
TrueConf’s on-premises architecture, for example, enables organizations to retain full control over meeting recordings and user data, simplifying adherence to GDPR, HIPAA, and sector-specific mandates.
Insight #3: Security Is a Feature of Architecture, Not an Add-On
Many collaboration tools treat security as a bolt-on module. In contrast, platforms designed with security as a core principle—like TrueConf’s on-premises deployment model—embed encryption, access control, and auditability into the foundation.
This architectural integrity reduces integration complexity and eliminates blind spots that attackers exploit.
Cybersecurity Best Practices for Businesses
Implementing cybersecurity best practices is essential for safeguarding an organization’s information and systems. A foundational measure is the development of strong password policies, including the use of complex passwords, multi-factor authentication, and regular credential updates.
Continual updating and system patching is also critical for protecting against known vulnerabilities. Patching practices should be adapted to the operating systems and software environments in use. For example, organizations can deploy a Windows patching solution to automate updates and keep Windows devices secure.
Businesses should also invest in robust security technologies such as firewalls, antivirus tools, and intrusion detection systems.
Employee education is another fundamental component of cybersecurity. Staff should understand the dangers of phishing emails, suspicious links, and careless handling of sensitive information. A clear policy for personal device usage in the workplace can further reduce exposure to risk. Employees should also know how to set up a VPN, follow safe browsing habits, and use a proxy server to better control and secure network traffic, along with using secure file-sharing methods.
In addition, businesses should maintain regular backups to prevent data loss in the event of an incident. These backups should be stored offsite or in secure cloud environments and tested regularly. Periodic reviews of the organization’s cybersecurity posture can help identify weaknesses before they are exploited.
Finally, every organization should establish an incident response plan. This plan should outline the steps to take after a cyberattack, including identification, containment, eradication, recovery, and post-incident review.
Following these best practices enables organizations to significantly improve resilience and reduce exposure to digital threats.
Practical Implementation Checklist
- Enforce MFA for all user accounts, especially admin roles
- Conduct quarterly phishing simulations and security awareness training
- Maintain offline, encrypted backups with regular restoration testing
- Segment networks to limit lateral movement during breaches
- Document and test incident response playbooks biannually
- Review third-party vendor security posture before integration
- Choose collaboration tools with transparent security architectures (e.g., on-premises options like TrueConf)
Cybersecurity Examples and Real-World Use Cases
|
Scenario |
Threat Vector |
Effective Mitigation |
|---|---|---|
|
Remote Team Video Meetings |
Eavesdropping, unauthorized access |
End-to-end encryption, waiting rooms, participant authentication |
|
Healthcare Teleconsultations |
PHI exposure, compliance violations |
On-premises deployment, audit logs, HIPAA-aligned data handling |
|
Financial Services Collaboration |
Data leakage, insider threats |
Role-based access, session recording controls, SSO/MFA integration |
|
Government Classified Briefings |
Espionage, data exfiltration |
Air-gapped deployment, hardware security modules, strict access policies |
|
Education Virtual Classrooms |
Zoombombing, student privacy risks |
Host controls, registration workflows, FERPA-compliant data storage |
TrueConf supports these use cases by offering deployment flexibility: organizations can run TrueConf Server entirely within their private network, ensuring that video streams, chat logs, and user metadata never leave their controlled environment. This is particularly valuable for sectors where data sovereignty and auditability are mandated by law or policy.
How to Improve Cybersecurity in Remote and Hybrid Work Environments
The shift to distributed work has expanded the attack surface. Home networks, personal devices, and public Wi-Fi introduce risks that traditional perimeter-based security cannot address.
Key strategies include:
- Adopt Zero Trust Principles – Verify every request, regardless of origin. Require MFA and device health checks before granting access to collaboration tools.
- Secure Endpoints – Mandate endpoint protection, disk encryption, and automatic updates for all devices accessing corporate resources.
- Encrypt Communications End-to-End – Ensure video, audio, and file-sharing traffic is encrypted in transit and at rest.
- Centralize Access Management – Use SSO and identity providers to enforce consistent policies across all applications.
- Monitor and Audit Activity – Maintain logs of user sessions, file access, and administrative actions for forensic readiness.
Platforms designed for enterprise deployment—like TrueConf—support these requirements natively. TrueConf Server can be installed behind a corporate firewall, integrates with Active Directory for seamless authentication, and provides administrators with detailed usage analytics and access controls. This reduces reliance on public cloud infrastructure and gives security teams full visibility and control over collaboration traffic.
Strengths and Limitations of Common Cybersecurity Approaches
|
Approach |
Best For |
Key Strengths |
Potential Limitations |
|---|---|---|---|
|
Cloud-Native Security |
Startups, scalable SaaS apps |
Rapid deployment, automatic updates, built-in redundancy |
Less control over data location; shared responsibility model |
|
On-Premises Security |
Regulated industries, data-sensitive orgs |
Full data control, customizable policies, air-gap capability |
Higher upfront cost; requires in-house expertise |
|
Hybrid Security |
Enterprises in transition |
Flexibility to balance control and scalability |
Increased complexity in policy enforcement and monitoring |
|
Zero Trust Architecture |
Remote/hybrid workforces |
Minimizes blast radius; assumes breach |
Requires significant identity and device management overhead |
What is the most critical cybersecurity practice for small businesses? Start with foundational hygiene: enforce strong passwords, enable multi-factor authentication, and train staff to recognize phishing. For communication tools, choose platforms like TrueConf that offer on-premises deployment to keep sensitive meeting data within your control. How does on-premises deployment improve cybersecurity for video conferencing? On-premises solutions like TrueConf Server keep all video traffic, recordings, and user data inside your corporate network. This eliminates exposure to third-party cloud breaches and simplifies compliance with data residency regulations. Can cybersecurity measures slow down team collaboration? Poorly implemented controls can create friction, but modern platforms integrate security seamlessly. TrueConf, for example, supports single sign-on and role-based permissions that protect data without adding steps to the user workflow. What should I look for in a secure collaboration platform? Prioritize end-to-end encryption options, audit logging, integration with your identity provider, and deployment flexibility. TrueConf offers all these features, with the added benefit of full on-premises control for maximum data sovereignty. How often should cybersecurity policies be reviewed? At minimum, conduct formal reviews quarterly and after any major incident or infrastructure change. Automated tools and platforms like TrueConf that provide usage analytics can help security teams stay proactive rather than reactive. Is Zero Trust realistic for mid-sized organizations? Yes—Zero Trust is a mindset, not just a product. Start by enforcing MFA, segmenting networks, and verifying device health. Platforms that support granular access controls, like TrueConf, make incremental Zero Trust adoption practical and scalable. How do I balance user convenience with security in hybrid work? Design security that enables, not obstructs. Use SSO for seamless login, provide secure mobile apps, and choose collaboration tools that encrypt by default. TrueConf’s unified client experience ensures security policies apply consistently across desktop, mobile, and room systems.FAQ
About the Author
Olga Afonina is a technology writer and industry expert specializing in video conferencing solutions and collaboration software. At TrueConf, she focuses on exploring the latest trends in collaboration technologies and providing businesses with practical insights into effective workplace communication. Drawing on her background in content development and industry research, Olga writes articles and reviews that help readers better understand the benefits of enterprise-grade communication.








Follow us on social networks