LDAP vs. Active Directory: What’s the Difference?
What Is LDAP?
LDAP (Lightweight Directory Access Protocol) is a protocol that implements Microsoft directory service (Active Directory) for Windows operating systems. LDAP is an industry standard, and is used by many organizations to store information about users, computers, and other objects.
The LDAP protocol is primarily concerned with the exchange of information between clients and servers. This information can include anything from user account details to contact information. LDAP is also used for directory services, which allow for the storage and retrieval of information in a central location.
What Is Active Directory?
Active Directory is a directory service that Microsoft developed for Windows networks. It provides a central location for managing users, groups, computers, and other network resources.
Active Directory also enables administrators to manage security, permissions, and other settings for network resources. The main purpose of Active Directory is to store user information in a centralized database. LDAP provides access to the database and authenticates local network users to access network resources.
Active Directory consists of objects, which are divided into three categories:
- People includes user groups and their accounts.
- Services may include email.
- Resources various equipment (scanner, printer, etc.).
The main purpose of Active Directory is to control and manage these objects, as well as to provide their data to external systems. Lightweight Directory Access Protocol includes a number of directory operations. To access them, you need to be connected to the corresponding network. Directory connection is performed by user authentication.
The next step in working with the Directory is using Search. This operation involves several parameters: the search base – that is where the data search begins, search depth – the area of the search, and the search filter – the selection of the Directory objects from the search area. Changing data is possible with the help of Modification operation. It includes adding, copying, moving and deleting accounts.
What Are Active Directory Forests, Trees, and Domains?
The Active Directory structure includes the main components:
- domain is a group of objects (users, computers, etc.). It is the main administrative unit of Active Directory. You can configure access rules and policies of interaction with other domains (trust relationships) for each domain.
- organizational unit (OU) is an optional and the smallest possible container. You can group domain objects (other containers, user accounts and computers) into this container if required. OU can be used to define group policies and administrative access for a set of resources within the same domain.
- domain tree is a collection of domains grouped in a hierarchical structure with a disjoint namespace.
- forest is a top-level container that includes all domains of each particular Active Directory instance.
Therefore, there must be at least one forest, one tree and one domain in the Active Directory hierarchy.
Each domain has at least one configured server with the role of domain controller, which runs AD services. This server stores domain object information and is responsible for catalog search, user login and authentication.
The domain controller that contains object data in AD forest is called a global catalog. This catalog stores a complete set of domain objects attributes and a partial replica of all other domains main attributes (the list of which can be customized) This allows the information to be quickly found regardless of its physical location on different domains.
The forest requires at least one global catalog. The first domain controller with the Active Directory domain services role is assigned by default. For LDAP and LDAPS protocols,TCP ports 3268 or 3269 are used to connect with the global catalog.
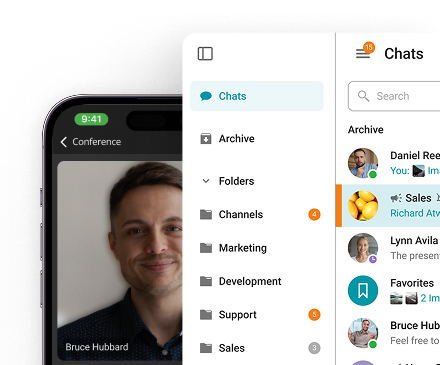
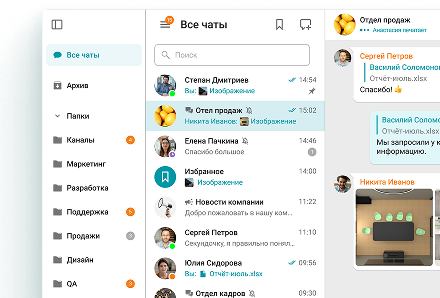
Connect your user directory to TrueConf Server and stop managing accounts manually
Securely integrate Active Directory and LDAP with TrueConf Server to automate user provisioning, enable single sign-on, and centralize access control across your corporate communications platform.
How Does Active Directory Work?
Active Directory services are a part of the Microsoft Windows Server operating system and are installed as one or more of its roles. The main role is Active Directory Domain Services (AD DS), which is used to organize all network objects into a secure logical structure.
The resulting hierarchical scheme is independent of objects’ physical location and network topology, which simplifies administration and access configuration. For example, a computer physical location change will not affect its role in the AD structure.
Active Directory operations include user authentication, as well as search, modification and comparison of objects. These functions are implemented using LDAP protocol.
Apart from AD DS, additional roles can be installed. These roles extend the use of AD: sensitive data encryption, single sign-on (it helps to avoid re-authenticating users to different web services on the network), etc.
Active Directory includes:
- Data repository is a part of the directory service that manages the storage and provisioning of information on each domain controller. Data is stored in a structured database (DB), otherwise called a catalog, which contains a set of all AD objects.
- Scheme is a set of class and object attributes (named parameters) definitions. The scheme standardizes data storage in a repository and thus allows to obtain information (for this purpose is used LDAP)
- Forests, trees, domains and organizational units are key elements of the AD logical structure, which were described in detail above.
Solutions like data catalog tools can help businesses streamline the management and organization of this structured information, ensuring efficient retrieval and security. Each of these objects belongs to a certain class (users, computers, domains, etc.) and have the same set of attributes.
Integration with DNS (Domain Name System) is used to convert the network resources names (computers, printers, etc.) registered in Active Directory structure into IP addresses. For example, this system allows users to access computers and allows computers to access domain controllers.
Each object in AD is an LDAP entry consisting of a set of attributes and their values, which fully describe it. For example, an object of class employee contains an email attribute that looks like: mail: user@example.com.
Example of the entire entry belonging to employee class:
dn: cn=John Smith,ou=employee,dc=example,dc=com
objectclass: employee
sn: Smith
cn: John Smith
mail: smith@example.com
ou: people
Pay attention to the value of the first attribute: cn=John Smith, ou=employee, dc=example, dc=com.
This is a Distinguished Name (DN), which identifies the entry within the forest and represents the full path from the AD root entry to the considered object. In this case, the entry containing information about employee John Smith is a subsidiary entry of organizational unit ou=employee, and its parent entry is the domain name example.com.
The values unique within its parent entry are called Relative Distinguished Name (RDN). For example, cn=John Smith is an RDN relative to ou=employee. The set of all RDNs in the form of a hierarchical chain is the DN of each entry. Attribute values can be used for AD object search filters, and DN values can be used to identify an object (for example, to modify it).
How Do LDAP & Active Directory Compare?
- LDAP (Lightweight Directory Access Protocol) is a protocol for accessing directory services to obtain data, while Active Directory is Microsoft’s implementation of directory services.
- Active Directory requires LDAP compliance to understand and respond to your request.
- Apart from Active Directory, there are other directory services, some of which are free of charge, such as OpenLDAP. Microsoft also developed Active Directory to go beyond LDAP and use other protocols such as Kerberus.
- Created in the 1980s and greatly improved since then, LDAP is a result of collaboration between telecommunications companies to create a protocol for transferring data from a server over TCP/IP.
- As LDAP is not tied to any company, it can be used in almost any operating system if you also have a directory service that can run in this operating system.
Active Directory is a Microsoft product that was originally developed based on LDAP to ensure its seamless operation and LDAP compliance. AD was originally designed to provide data via LDAP, but has expanded to include other services as mentioned above.
On the other hand, the Microsoft-owned Active Directory is usually located in the Windows operating system, which is also owned by Microsoft. The well-known Windows cannot be used directly in Active Directory, as there are many other choices for consumers.
In conclusion, Active Directory is one of the solutions that can provide services that use LDAP. LDAP, on the other hand, is a protocol and therefore it’s more common than Active Directory. Whether you use Active Directory, or OpenLDAP, or any other directory service offering from other companies, you will still probably use LDAP.
Summary:
- LDAP is a protocol for retrieving information from a directory service such as Active Directory.
- LDAP is much older than Active Directory, and most of Active Directory comes from LDAP.
- Active Directory is a Microsoft solution, while LDAP is the result of industry efforts.
- The active directory is usually rarely located outside of the Windows operating system.
- Active Directory provides additional services beyond LDAP-like functionality.
What Are the Benefits of Using Active Directory/LDAP in Video Conferencing?
The participants may be “scattered” around different places (different cities, countries and even continents) during a video conference. The number of users may vary from a few to several hundreds. Active Directory/LDAP makes the work of the administrator who provides services to the corporate directory users much easier.
Connecting to the LDAP server helps the administrator to avoid re-establishing records and it saves his time. Users, in their turn, get rid of the re-authorization session. Active Directory/LDAP allows the use of the existing authorization mechanism on a video conferencing terminal, without the need to re-enter login and password when starting a session. If LDAP is used in a local network, a user will be able to connect and authenticate to any computer in the corporate network.
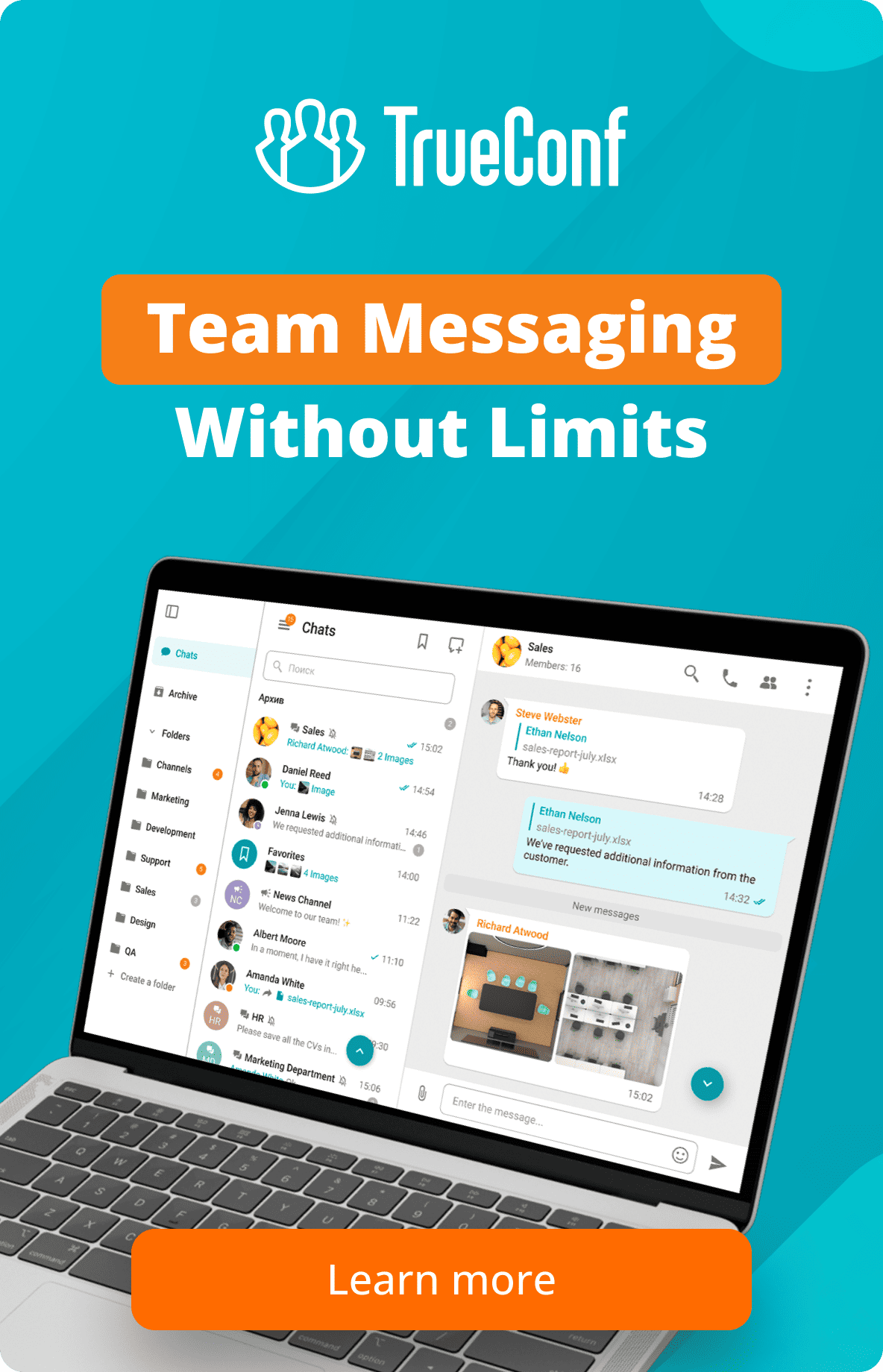
Strengthen security and simplify user management with TrueConf & Active Directory.
Integrate LDAP or Active Directory with TrueConf Server to enforce corporate policies, control access from a single directory, and ensure every employee connects securely — without extra admin workload.








Follow us on social networks