HIPAA Video Conferencing Solutions for Healthcare

Virtual healthcare adoption keeps accelerating, driven by patient demand, better connectivity, and proven efficiency gains. As clinical consultations shift toward digital platforms, securing sensitive patient data grows essential. Security frameworks must advance alongside telehealth expansion to preserve trust and satisfy regulatory mandates.
HIPAA Regulatory Framework for Providers Vendors
HIPAA sets U.S. national standards for health information security. Covered entities (hospitals, clinics, practices, insurers) and their business associates (vendors) must adopt three safeguard categories: administrative (policies or training), technical (encryption or authentication), and physical (facility or device protection).
These measures guarantee data confidentiality, integrity, and authorized access throughout its entire lifecycle. Any video system utilized for telehealth must meet these comprehensive requirements to legally process PHI.
PHI in Digital Healthcare
HIPAA regulates electronic PHI from creation until disposal. For video conferencing, this covers all virtual visit audio or video streams, screen shares, chats, recordings, and metadata (timestamps, participant lists, connection details). Systems must ensure ePHI stays confidential, unaltered, and accessible only to authorized care personnel.
Privacy & Security Rules Overview
The Privacy Rule controls data usage; the Security Rule requires specific ePHI protections via technical, administrative, and physical safeguards. For video platforms, this means encrypted transmissions, restricted archive access, activity logging, participant verification, and periodic security assessments, applicable regardless of organization size.
Covered Entities vs. Business Associates
Covered entities (providers, insurers) hold primary responsibility for patient data. Business associates (vendors like video platforms) process PHI on their behalf and must: meet HIPAA security standards, limit access, report incidents promptly, and execute a BAA. Without a signed BAA, clinical use involving PHI is legally forbidden.
Technical Security Measures
HIPAA’s technical safeguards shield electronic PHI through deliberate system architecture, precise access limitations, and continuous surveillance of data usage. For healthcare video conferencing, these protections span the entire virtual consultation space: user authentication, instant messaging, file sharing, session archiving, and comprehensive activity tracking for compliance and forensic review.
This approach ensures every potential vulnerability point has security measures matched to clinical information sensitivity.
Encryption During Transmission & Storage
Video appointments require strong encryption across all transmission stages. Quality implementations employ Transport Layer Security (TLS) for signaling and Secure Real-Time Transport Protocols (SRTP) for media streams to block eavesdropping or interception. Equally critical is encrypting stored data: recordings, transcripts, metadata, and audit records must utilize industry-standard cryptographic methods.
Encryption keys need protection through hardware security modules (HSMs) or strengthened key management systems, with access limited to authorized staff following least-privilege principles.
Secure Transmission Protocols
Protected video communications require resilient protocols preventing interception, content modification, or man-in-the-middle attacks. Implementation demands current cryptographic standards with sufficient key lengths, elimination of vulnerable outdated ciphers, and authenticated session establishment verifying participant identities.
Platforms should incorporate secure onboarding features: algorithmically generated meeting identifiers, time-limited invitation links expiring after session initiation, and mandatory identity verification to prevent unauthorized access through layered security measures.
Audit Logging & Activity Tracking
HIPAA mandates comprehensive documentation of all system interactions with electronic PHI. Effective logging records authentication attempts with timestamps and IP addresses, session initiation or conclusion times, participant lists with roles, administrative modifications, and all access to recordings or exported materials.
These records support regulatory audits and security incident investigations. Logs should enable efficient searching, export in standard formats, include cryptographic protection against alteration, and satisfy retention requirements aligned with organizational policy and regulations.
Role-Based Access & Session Management
Telehealth systems must enforce access restrictions based on organizational role and clinical necessity, assigning permissions matched to each user’s duties without excessive privileges. Practical session management includes: virtual waiting rooms for patient admission control, session lockdown preventing late entries, detailed screen-sharing permissions, role-based messaging and file exchange restrictions, real-time participant removal for unauthorized attendees, and configurable recording permissions preventing unintended capture of sensitive conversations.
Together, these mechanisms reduce unauthorized PHI exposure during consultations while minimizing risks from human error or configuration mistakes.
Administrative Safeguards
Administrative safeguards form the organizational foundation for technical protections, emphasizing governance, personnel management, and systematic approaches that maintain HIPAA compliance tools through ongoing improvement. Even sophisticated video conferencing technology fails if employees lack proper training or internal protocols have weaknesses creating exposure risks.
These safeguards integrate information security into daily operations and organizational culture rather than treating it as a one-time technical installation. Through intentional policies, continuous education, and methodical risk management, administrative safeguards build organization-wide compliance capable of adapting to emerging threats and regulatory updates.
Employee Training & Compliance Policies
All healthcare personnel need comprehensive, role-specific education on secure PHI management for both in-person and virtual care. Effective programs address: secure authentication and password standards, multi-factor verification and device management, secure session invitation distribution, screen sharing and document exchange protocols, policies for organizational and personal device usage, and privacy protections for remote work environments.
Organizations must maintain accessible written policies covering platform usage, access procedures, data retention periods, and consequences for noncompliance. Regular refresher training with simulated exercises ensures staff stay current with emerging threats, security methods, and regulatory updates.
Risk Assessments
HIPAA requires recurring risk analyses to identify vulnerabilities across all systems handling electronic PHI. For telehealth, evaluations should examine: platform security configurations, endpoint protection on clinician and patient devices, network controls including firewalls and VPNs, authentication workflows, and procedural gaps that might expose patient information through human error.
Vulnerability assessments cannot be one-time activities. They require scheduled repetition and must trigger when significant changes occur — new platforms, expanded remote work, additional third-party services, or emerging threat intelligence — to ensure continuous identification and timely remediation of evolving vulnerabilities.
Incident Response Planning
Since no system guarantees complete breach immunity, healthcare institutions must maintain documented incident response procedures. These should specify: incident detection through monitoring and user reporting, internal escalation pathways with defined timeframes, assigned roles during investigations, patient notification methods consistent with regulations, and mandatory reporting timelines to authorities under HIPAA’s Breach Notification Rule.
Well-structured protocols minimize patient impact, ensure regulatory compliance to avoid additional penalties, and demonstrate organizational diligence. Regular tabletop simulations and mock breach scenarios enable staff to practice responses, identify protocol gaps, and refine procedures before actual incidents, building organizational resilience and crisis management confidence.
Business Associate Agreements (BAA)
A Business Associate Agreement is a legally binding contract between a healthcare provider (covered entity) and a service vendor (business associate) that handles Protected Health Information. In telehealth, any video conferencing provider storing, processing, or transmitting patient data during consultations qualifies as a business associate and must sign a BAA before clinical use.
Without a properly executed BAA, a platform is legally prohibited for clinical consultations involving PHI, regardless of advertised security features. This isn’t bureaucratic overhead: it’s a fundamental legal mechanism establishing accountability, defining shared responsibilities, and creating enforceable obligations for protecting sensitive health data.
Why Are BAAs Required?
BAAs are statutorily mandated under HIPAA because they formally establish vendor obligations to protect patient information, specify consequences for noncompliance, and mandate immediate notification upon discovering unauthorized PHI access. Critically, HIPAA prohibits healthcare organizations from transferring their fundamental compliance responsibility to vendors, the covered entity retains ultimate accountability under federal law.
The BAA establishes a documented understanding of each party’s roles and obligations. Platforms whose vendors refuse to sign a BAA cannot legally be used for clinical consultations involving PHI; marketing terms like “HIPAA-ready” or “HIPAA-friendly” hold no legal validity without an executed agreement.
What to Verify in Vendor BAAs?
Before signing, healthcare organizations must carefully review BAA provisions to verify the vendor’s responsibilities. The agreement should explicitly specify: which PHI categories will be processed, how information will be handled, retained, transmitted, destroyed, and which security controls the vendor commits to implementing.
For cloud or hybrid deployments, the BAA must clearly delineate duty divisions between provider and vendor, clarifying who manages endpoint security, access governance, encryption keys, patching, and vulnerability scanning. This prevents responsibility gaps that could create compliance vulnerabilities or complicate incident response.
Essential Features for HIPAA-Compliant Video Conferencing
Organizations evaluating telehealth platforms should prioritize: genuine end-to-end encryption with decryption keys held only by session participants, robust access governance with multi-factor authentication and single sign-on, and seamless EHR integration via secure APIs to eliminate manual data entry.
Essential features include automated scheduling with secure, time-limited invitations, configurable virtual waiting rooms, and encrypted real-time messaging. Clinical effectiveness demands reliable audio or video transmission, while intuitive interfaces reduce adoption barriers for providers and patients with limited tech familiarity.
For recording capabilities, platforms must enforce encrypted archival with strict access restrictions, role-based retrieval limits, and configurable retention policies aligned with legal mandates.
End-to-End Encryption
Authentic end-to-end encryption ensures audio, video, shared materials, and texts remain accessible only to authorized participants throughout transmission and storage. When properly implemented, even the platform provider cannot decrypt session content, delivering maximum confidentiality against external and internal threats.
Organizations should validate encryption across all client implementations (desktop, mobile, browser) and confirm protection extends to screen sharing, document transfers, and metadata, not just primary audio or video channels. Documentation of encryption standards and independent security audits provides additional validation.
Strong Access Control & Authentication (MFA, SSO)
Multi-factor authentication (MFA) and single sign-on (SSO) significantly reduce unauthorized access risk by requiring multiple verification elements beyond passwords. Clinical platforms should enforce password complexity requirements, support device-level authentication, and implement identity validation aligned with organizational frameworks.
Additional protections include: session auto-lock after inactivity, granular permission structures limiting capabilities to role-appropriate functions, and virtual waiting areas requiring clinician approval before patient entry. These features reduce inadvertent PHI exposure while supporting efficient workflows.
EHR or EMR Integration
Direct interoperability with Electronic Health Record systems optimizes clinical operations while minimizing error-prone manual transcription. Integrating specialized solutions like cardiology ehr software further enhances data accuracy, streamlines cardiology workflows, and supports more efficient patient care delivery within telehealth environments. Secure APIs facilitate protected exchange of appointment data, patient context, clinical documentation, and post-encounter summaries between video platforms and primary clinical systems.
Integrations should include comprehensive audit trails, adhere to data minimization principles by transferring only essential information, and support configurable access rules limiting PHI exposure to authorized personnel. Security testing during vendor evaluation helps identify vulnerabilities before deployment.
Scheduling & Appointment Management
Healthcare-optimized platforms like TherapyStack and others typically include embedded scheduling with automated patient notifications, configurable virtual waiting rooms, and invitation distribution through encrypted channels rather than public calendars.
Advanced capabilities include: time-restricted access links expiring after session start, structured patient intake workflows collecting pre-encounter information, and clinician-controlled admission preventing unauthorized entry. These features improve appointment adherence and reinforce privacy throughout the consultation lifecycle.
Secure Messaging & Chat
Encrypted real-time messaging enables clinicians to transmit instructions, resources, and follow-up guidance during sessions without compromising PHI confidentiality or creating unsecured channels outside the protected platform.
Valuable features include: granular controls determining which roles may initiate file transfers, configurable message retention policies aligned with compliance requirements, and administrative options to disable messaging when specific protocols or patient preferences mandate such restrictions.
High-Quality Video & Audio
Clinical effectiveness depends on reliable audio clarity and visual fidelity, particularly during physical examinations, behavioral health sessions where nonverbal cues matter, and progress evaluations tracking clinical outcomes.
Platforms should demonstrate adaptive bandwidth technology adjusting to network conditions, robust connection resilience preventing mid-session disruptions, and uniform performance across desktop, mobile, and browser interfaces.
Ease of Use for Providers and Patients
User-centered design minimizes technical barriers for healthcare professionals and patients, directly influencing adoption rates and telehealth satisfaction. This is especially critical for elderly patients, individuals with disabilities, or those with limited tech proficiency.
Usability-enhancing features include: browser-based access eliminating complex installations, straightforward onboarding with clear guidance, minimal download requirements, and streamlined session joining processes. User testing with representative populations during evaluation helps identify gaps before organization-wide deployment.
Best HIPAA-Compliant Video Conferencing Platforms
The following platforms have achieved widespread adoption across healthcare environments and provide configurations supporting HIPAA compliance. Access to HIPAA-compliant capabilities generally depends on selecting appropriate service tiers, correctly configuring security settings, and executing a Business Associate Agreement where required by the vendor.
TrueConf Server
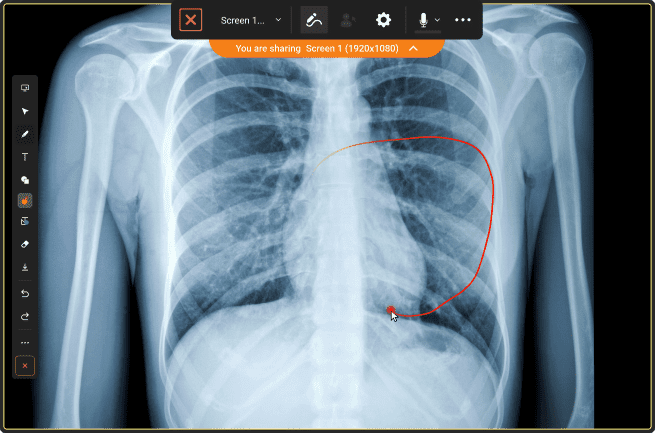
A flexible on-premises and hybrid video conferencing solution enabling healthcare organizations to maintain complete authority over their telehealth infrastructure by hosting servers within their own secure, compliant data environments.
HIPAA & Security Attributes:
- Complete on-premises deployment option for maximum data sovereignty and infrastructure governance
- End-to-end encryption protecting all communication channels including video, audio, messaging, and file exchange
- Full organizational control over data storage locations, retention timelines, and secure disposal procedures
- Native interoperability with internal authentication frameworks including LDAP, Active Directory, and SSO providers
- Business Associate Agreement availability dependent upon appropriate contractual arrangements and service tier selection
Empower your telemedicine experience with TrueConf!
Zoom for Healthcare
A purpose-built cloud telehealth solution developed specifically for medical institutions and clinical practices with healthcare-specific compliance configurations.
HIPAA & Security Attributes:
- Executable Business Associate Agreement available for covered entities
- AES 256-bit encryption standards for information protection during transmission and in storage
- Configurable virtual waiting areas and comprehensive session management controls
- Granular role-based access governance aligned with clinical workflow requirements
- Administrative controls for recording management and audit log access
Doxy.me
A streamlined, browser-native telehealth platform emphasizing accessibility and ease of use without compromising foundational security requirements.
HIPAA & Security Attributes:
- Business Associate Agreement provided upon request for healthcare customers
- End-to-end encrypted consultation sessions protecting audiovisual content
- Zero-download architecture enabling immediate patient access via standard web browsers
- Integrated virtual waiting room functionality preserving patient privacy pre-session
- Simple interface designed for patients with limited technical proficiency
Webex for Healthcare
Cisco’s enterprise communication infrastructure adapted specifically for clinical environments and healthcare workflow integration requirements.
HIPAA & Security Attributes:
- Comprehensive Business Associate Agreement support for covered entities
- Optional end-to-end encryption for maximum data protection in sensitive consultations
- Advanced enterprise identity management integration with existing organizational directories
- Robust administrative controls for policy enforcement and audit capabilities
- Global infrastructure supporting healthcare organizations with international operations
RingCentral for Healthcare
A unified communications ecosystem incorporating secure video conferencing capabilities alongside telephony and messaging functions tailored for clinical settings.
HIPAA & Security Attributes:
- Executable Business Associate Agreement available for healthcare customers
- Comprehensive encryption protecting data both during transmission and while stored
- Rigorous authenticated user access controls preventing unauthorized platform entry
- Integrated scheduling and patient management features supporting clinical workflows
- Administrative dashboards for compliance monitoring and policy management
Pexip Health
A highly scalable telehealth video platform distinguished by exceptional interoperability across diverse healthcare systems, legacy equipment, and varied clinical environments.
HIPAA & Security Attributes:
- Secure, encrypted meeting bridge architecture supporting multi-party clinical consultations
- Comprehensive encryption protocols safeguarding all communications and shared content
- Flexible deployment models supporting public cloud, private cloud, or on-premises infrastructure based on organizational requirements
- Advanced integration capabilities with EHR systems and clinical workflow tools
- Granular administrative controls for compliance management and audit support
GoTo (GoTo Meeting)
A business-oriented video conferencing solution enhanced with healthcare-specific compliance configurations and administrative controls for clinical utilization.
HIPAA & Security Attributes:
- Business Associate Agreement availability for healthcare deployments and covered entities
- Encrypted session technology protecting consultation content from interception
- Granular identity verification and access control mechanisms for participant management
- Configurable recording options with secure storage and access controls
- Administrative tools for policy enforcement and compliance documentation
VSee
A telehealth platform architected specifically around clinical workflow requirements rather than generic communication needs, with healthcare compliance as a foundational design principle.
HIPAA & Security Attributes:
- Encrypted session technology protecting all transmitted data including video, audio, and files
- Backend infrastructure designed and maintained to align with HIPAA regulatory requirements
- Secure file transfer capabilities enabling protected exchange of clinical documentation and images
- Lightweight client architecture supporting diverse devices and network conditions
- Clinical workflow features supporting remote examination and consultation needs
Thera-Link
A specialized telehealth solution engineered specifically for mental health practitioners and behavioral healthcare professionals with workflow features tailored to therapy contexts.
HIPAA & Security Attributes:
- Business Associate Agreement support for clinical practices and covered entities
- Encrypted video sessions ensuring patient confidentiality during therapeutic interactions
- Integrated patient management tools including scheduling, clinical notes, and treatment planning
- Secure messaging functionality for between-session communication
- Compliance-focused design supporting mental health privacy requirements
SimplePractice Telehealth
A comprehensive practice management system featuring embedded telehealth capabilities designed for small clinics, group practices, and independent practitioners.
HIPAA & Security Attributes:
- Encrypted video communications protecting session content from unauthorized access
- Secure patient portal enabling protected information exchange outside consultation hours
- Infrastructure architecture aligned with HIPAA security and privacy requirements
- Integrated scheduling, billing, and documentation tools reducing workflow fragmentation
- Automated compliance features supporting small practice operational needs
Best Practices for Implementing HIPAA-Compliant Video Conferencing
Successfully deploying telehealth video solutions requires more than technical setup: it demands comprehensive operational protocols and security practices that mitigate risk, maintain compliance, and encourage consistent adoption across teams. These guidelines outline essential measures healthcare organizations should implement when launching telehealth initiatives to build a secure, sustainable virtual care environment.
Conduct a Risk Assessment
Perform a thorough evaluation of technical infrastructure, network security, endpoint devices, and clinical workflows to identify vulnerabilities before deployment. This should cover provider-owned devices (laptops, smartphones), wireless network protections, and all third-party integrations that may create data exposure pathways.
Document findings, prioritize remediation by risk severity, and establish timelines for addressing gaps. Reassess regularly and whenever significant changes occur to infrastructure, workflows, or the threat landscape.
Train Staff on HIPAA & Platform Usage
Ensure all staff receive role-appropriate instruction on security policies, session management procedures, patient privacy requirements, and protocols for reporting suspected incidents or violations. Training should address common high-risk errors: publicly sharing session links on social media, recording sessions without proper authorization or consent, conducting consultations in non-private environments, and mishandling shared files or screen content containing PHI.
Configure Secure Policies
Establish organization-wide security policies mandating multi-factor authentication, role-based access restrictions aligned with clinical responsibilities, and explicit controls for session recording permissions, storage procedures, and authorized access. Where possible, standardize security settings through centralized administrative policies rather than relying on individual user configurations that may introduce inconsistencies or unintended exposure pathways.
Verify Patient Identity
Implement reliable authentication methods to verify patient identity before consultations, especially critical during initial encounters, when discussing sensitive health information, or when prescribing controlled substances.
Verification approaches may include: knowledge-based questions from patient records, secure patient portal login confirmation, video-based identity verification comparing appearance to record photographs, or other validation techniques appropriate to the clinical context and risk level.
Educate Patients on Privacy
Provide patients with clear guidance encouraging virtual consultations from private spaces using secure internet connections rather than public Wi-Fi networks vulnerable to interception. Recommend practical privacy behaviors: using headphones to prevent audio leakage, ensuring room privacy before sessions, avoiding shared or public devices for telehealth access, and understanding their rights regarding recording, data usage, and information sharing under HIPAA.
FAQ
What makes a video conferencing platform HIPAA-compliant?
For a video conferencing tool to be considered HIPAA-compliant, it must actively enforce the full range of protective measures outlined in the HIPAA Security Rule. This involves a combination of administrative procedures, physical security controls, and technical safeguards working in unison.
Key technical requirements generally involve strong encryption for data both in transit and at rest, strict access controls to limit information visibility to authorized staff, detailed audit trails tracking all actions involving Protected Health Information (PHI), secure login protocols like multi-factor authentication, and, most importantly, the provider’s readiness to sign a legally binding Business Associate Agreement (BAA).
Crucially, software features alone do not guarantee compliance. It relies heavily on how the healthcare provider configures the platform, oversees user access rights, trains staff, and embeds the tool into daily medical practices. Achieving regulatory alignment is a shared responsibility between the technology vendor and the healthcare organization.
Do all telehealth platforms automatically meet HIPAA requirements?
Not necessarily, most telehealth applications do not satisfy HIPAA standards out of the box. Many apps built for general consumers miss essential security measures needed for medical settings and often refuse to sign Business Associate Agreements, making them unlawful for handling PHI.
Moreover, even platforms advertised as “HIPAA-compliant” often need specific settings adjustments to ensure true regulatory adherence. This involves enabling encryption, restricting access rights, turning off public meeting links, and setting up secure recording rules. It is up to healthcare providers to independently check a vendor’s compliance status, review contract details, and verify system settings before using any tool for patient appointments.
Is a Business Associate Agreement required?
Absolutely. A Business Associate Agreement is a legal mandate whenever a third-party vendor processes, keeps, or sends Protected Health Information for a HIPAA-covered entity. This contract outlines the vendor’s duties regarding data safety, sets rules for breach reporting and incident response, defines liability for violations, and controls data handling from start to finish.
Without an executed BAA, using a platform for clinical tasks involving PHI is illegal, no matter how advanced its technology or encryption is. Covered entities cannot bypass this rule through waivers or assumptions; contractual accountability is non-negotiable.
What are the limitations of standard video tools in medical settings?
General-purpose communication platforms built for business or personal use lack the specialized safeguards needed for medical information under privacy statutes. Most mainstream solutions refuse to sign Business Associate Agreements (BAAs), a HIPAA mandate for any vendor handling patient data. They depend on basic encryption instead of healthcare-specific security protocols and exclude advanced access controls vital for clinical workflows.
These platforms frequently enforce data retention policies clashing with healthcare regulations and usually omit permanent audit trails required for compliance audits and security reviews. Lacking these protections, providers risk exposing Protected Health Information (PHI), possibly triggering heavy fines, legal proceedings, and eroded patient trust.
What is protected health information (PHI)?
PHI includes any health-related data linked to a specific individual: personal identifiers, medical history, diagnostic results, laboratory findings, and billing details. This constitutes the foundation of federal healthcare privacy legislation. Unauthorized access or disclosures can harm patients through identity fraud, financial scams, discriminatory actions, or emotional distress.
For healthcare organizations, violations result in monetary penalties, mandated remediation steps, and reputational damage. Protecting this data represents both a legal duty and moral obligation, not just a technical consideration.
Can HIPAA-compliant platforms integrate with EHR systems?
Many video platforms that support HIPAA standards allow secure connectivity with Electronic Health Record (EHR) and Electronic Medical Record (EMR) systems via encrypted APIs and standard integration methods. These links streamline clinical workflows by allowing synchronized scheduling, automatic patient data filling, easier documentation, and sharing of visit summaries without manual input.
However, such integrations bring extra compliance duties. Organizations must ensure data sharing follows the “minimum necessary” rule, exchanging only what is needed for care. They must also set up role-based access controls to manage data transfers between systems and keep detailed audit logs of all interactions to meet regulatory standards and aid in any future investigations.
What are the penalties for HIPAA violations during video visits?
Violations during telehealth sessions can lead to various enforcement actions based on the breach’s severity, cause, and the organization’s reaction. Consequences may include mandatory corrective action plans, civil fines ranging from $100 to $50,000 per violation (with yearly caps over $1.5 million for repeated issues), and possible criminal charges involving jail time for cases of willful neglect or intentional abuse.
Aside from legal and financial costs, organizations often suffer reputational damage, loss of patient trust, higher malpractice insurance rates, stricter future audits, and a competitive edge loss in markets where security is a key decision factor for patients and partners.
Are international video conferencing vendors permitted under HIPAA?
HIPAA rules do not explicitly ban working with international tech vendors or storing data outside the U.S. However, covered entities remain fully responsible for ensuring any vendor handling PHI, regardless of location or structure, follows all HIPAA rules and signs a valid Business Associate Agreement.
Providers must perform strict due diligence on data storage sites, assess risks linked to cross-border data transfers under foreign laws, and check for conflicts with regulations like the EU’s GDPR. Ultimately, the healthcare organization holds legal liability for PHI protection even if data is stored on foreign servers or accessed by staff outside the United States.
How should session recordings be handled securely?
If recording telehealth sessions is needed for clinical, training, or regulatory reasons, organizations must apply strict security measures throughout the recording’s lifecycle, from creation to secure disposal. Recordings must be encrypted using standard methods during storage and transmission. Access should be strictly limited to authorized staff with a valid clinical or administrative reason.
Every access attempt, whether successful or not, must be recorded in secure logs showing who accessed the data, when, and what action was taken. Organizations also need clear policies on when recording is allowed, must get and document patient consent before recording, define secure storage spots meeting retention rules, and use certified deletion methods to ensure permanent data erasure once retention periods end.
About the Author
Diana Shtapova is a product specialist and technology writer with three years of experience in the unified communications industry. At TrueConf, she leverages her deep product expertise to create clear and practical content on video conferencing platforms, collaboration tools, and enterprise communication solutions. With a strong background in product research and user-focused content development, Diana helps professionals and businesses understand core product features, adopt new technologies, and unlock the full potential of modern collaboration software.








Follow us on social networks