BYOD Benefits and Video Conferencing Security in India
What is BYOD?
BYOD, or Bring Your Own Device, is a workplace policy that allows employees to use their personal laptops, smartphones, or tablets for professional tasks instead of company-issued hardware. In the context of video conferencing, BYOD simplifies the process by letting users connect from familiar devices with minimal setup. According to Barco, this approach can save employees up to 58 minutes per day by enabling quicker meeting starts and a more intuitive experience.
Most businesses today use the BYOD concept in one way or another, as it has many advantages. However, companies often implement such practices without sufficient preliminary analysis and risks. As an expert in the field of corporate communications, TrueConf would like to inform its clients about both the potential problems and the advantages of BYOD.
How does BYOD work?
Initially, the company needs to establish a clear security policy for each device to ensure secure connections to the corporate network.
For example, a document that delineates the norms, limitations, and prerequisites:
- Minimum security measures: Enable data encryption on all devices to protect confidential information from unauthorized access. Create strong passwords to prevent hacking attacks and data leaks
- Types of corporate data for storage on local devices: Distributed files and documents that do not require a constant network connection can be saved on local devices for convenient access and work.
- Application of timeout controls and automatic lock functions: Setting up automatic device locking after a certain period of inactivity. Configuring timeouts for device sessions to protect information in case the device is lost.
- Mobile device management (MDM) on BYOD: Unified endpoint management and MDM for BYOD encompass automated threat evaluations on devices, consistent security upgrades, remote deployment of updates, and the ability to lock or erase data from a device when necessary remotely.
- Automatic remote data wiping: Establish a policy to remotely wipe sensitive data from employee devices in the case of gadget loss, termination, or breach of security policy.
- Organization type: Financial and healthcare institutions require heightened security measures due to the confidentiality of their data, while smaller companies can use less stringent security protocols.
Automatically scanning BYOD devices for potential threats include the capacity to prevent harmful applications from accessing the corporate network.
Make BYOD Safe and Secure with TrueConf
Enable your team to use personal devices without sacrificing security. TrueConf offers ultra HD meetings, self-hosted deployment with no internet required, and full control over your data.
What level of access does BYOD offer?
Once the security policy is in place, organizations must outline the guidelines for integrating BYOD devices into business operations. These guidelines encompass best practices for managing data access, securing devices, and ensuring compliance with company protocols to streamline documentation and enhance operational efficiency.
- Defining permissible applications for access from personal devices.
- Establishing access rules for corporate applications and data from user devices.
- Prohibiting the storage and transmission of restricted materials or the use of devices for impermissible non-business purposes.
There are 3 levels of primary access
- Entry-Level Access: Employees are allowed to use personal devices for accessing company resources.
- Restricted Access: Employees have the ability to access certain data and applications on their personal devices, which are protected by security features.
- Complete Access: Employees have unimpeded access to corporate resources and sensitive data.
Ultimately, BYOD strategies should incorporate a defined procedure for employee departures, regardless of the circumstances. This procedure should encompass HR and network directory protocols, in addition to a BYOD offboarding checklist. The checklist should include deactivating work email accounts, deleting company data from devices, thoroughly wiping data from corporate devices, and updating shared passwords for corporate accounts.
Advantages of BYOD
- It’s convenient. Employees don’t have to worry about using corporate devices because they have well-known devices.
- Budget savings. It is possible for companies to save up to $341 per employee per year if they switch to a Bring Your Own Device model.
- Performance improvement. The use of familiar devices, configured according to employees’ preferences, leads to an increase in productivity.
- Mobility. While staying connected to the network, employees can access work documents from their personal mobile devices.
- Reduced training time for employees. Training can increase the time it takes for a new employee to adapt to a new system.
Disadvantages of BYOD
- Each device linked to the corporate network by an employee presents a potential vulnerability to malware, leading to corporate data exposure.
- Due to strict regulations and fines, the practice of Bring Your Own device can’t be implemented in certain industries such as healthcare, finance, and government administration.
- Specific security measures will be required for different device types and operating systems.
- A personal device with corporate data can be lost or stolen.
- Compatibility issues with corporate applications may be caused by various devices and operating systems.
Our Advice
Make sure to protect your corporate data by selecting BYOD applications which provide sufficient security. Every business application should require an obligatory sign-in and security authorization from the employee before every work session. The application must also ensure the availability of mandatory defense protocols (SSL/TLS) and traffic signal encryption (AES-256 or GOST) when connecting to corporate resources.
It is essential to have certain corporate rules governing remote work with business applications, such as the restricting the use of employees’ devices within a closed corporate network. This will significantly reduce the risk of information leakage. For IT professionals managing device and application security, certifications like Microsoft Endpoint Administrator using MD-102 Exam Dumps can be highly beneficial. It will help them gain expertise in configuring and securing BYOD policies effectively. Enforcing the use of a locking system on a device (such as a PIN, password or unlock pattern) will also increase security.
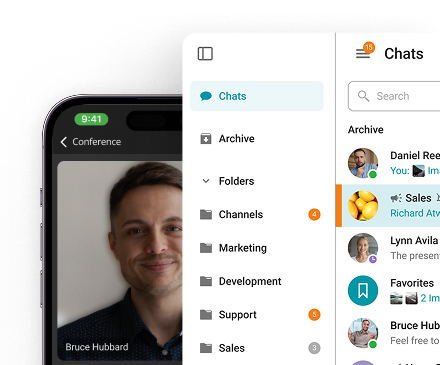
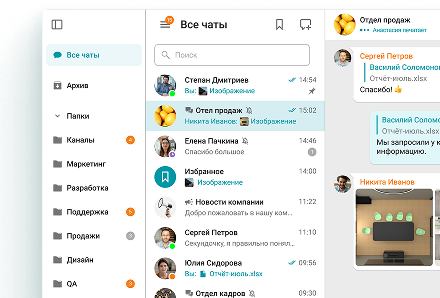
BYOD Security in TrueConf Solutions
One of the top benefits of TrueConf products are the built-in security features. TrueConf BYOD solutions are among the safest on the market because they were originally designed for use in private networks without needing to connect to the Internet. In this case, it is enough to open a single TCP port for network administrator to maintain proper TrueConf operation.
By default, all connections between client applications and other TrueConf solutions are installed in secure mode (SSL), and the transmitted data is encrypted using advanced algorithms, such as AES-256. The use of complex and efficient algorithms and proprietary codecs for compression and transmission of information does not allow the interceptor to reproduce it using standard protocols and codecs.
When considering whether or not to implement BYOD in your workplace, it is important to remember that, while including many benefits, it also entails certain risks. By creating an implementation plan, researching and enforcing corporate security, and selecting the right applications and devices, you can reduce the risks and increase the rewards found in increased employee satisfaction and a streamlined workflow.
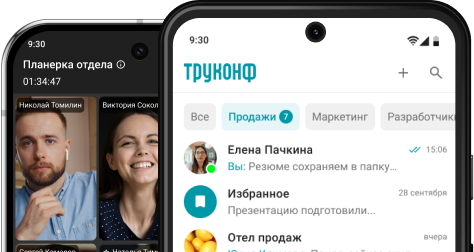
Kudremukh Iron Ore Limited (KIOCL)|Case Study
KIOCL provided their employees with secure tools for collaboration, video calls, and team messaging by implementing TrueConf Server. An autonomous system unified more than 1,000 employees allowing to facilitate work meetings in hybrid and online modes from any location.

We hope that our article will help you make the right conclusions about BYOD.
About the Author
Nikita Dymenko is a technology writer and business development professional with more than six years of experience in the unified communications industry. Drawing on his background in product management, strategic growth, and business development at TrueConf, Nikita creates insightful articles and reviews about video conferencing platforms, collaboration tools, and enterprise messaging solutions.









Follow us on social networks