# Network and federation settings, STUN/TURN servers
Here are the minimum steps needed to set up a working corporate communication system:
Select a machine (PC, physical or virtual server) with suitable hardware.
Configure HTTPS (it is used for many key features such as integration with the AI server, conference scheduling, etc.) and specify the external server address (the address of the guest page).
Configure the server availability for the users within the corporate network and, if necessary, for the users from an external network (outside the secure corporate network). ◀️ You are here!
Create user accounts or integrate the server with a directory service via the LDAP/LDAPS protocol.
Install client applications for users and show them how to connect to your server (check the documentation for the desktop application).
In the Network → Network settings section you can configure some network settings for your TrueConf Server instance:
connecting client applications and third-party devices (SIP, H.323, etc.)
sending email notifications for users and administrator
connecting to other TrueConf Server instances.
# Network Settings
In the section Network → Network settings, you can specify the IP addresses and ports that client applications downloaded from TrueConf Server will use, when trying to connect to the server. By default, client applications will use only the IP address of the machine where TrueConf Server is installed.
Client applications always connect to TrueConf Server over the only TCP port (4307is used by default). It is the only port used for signalling, sending authentification data and audio or video streams. An HTTPS port (443 selected by default) is used for displaying the scheduler, accessing real-time meeting management and for API calls. To learn more about this topic, check out the article in our knowledge base.
You can specify a different port when editing the list of IP addresses.
No UDP port can be used for communication between TrueConf Server and a client application.
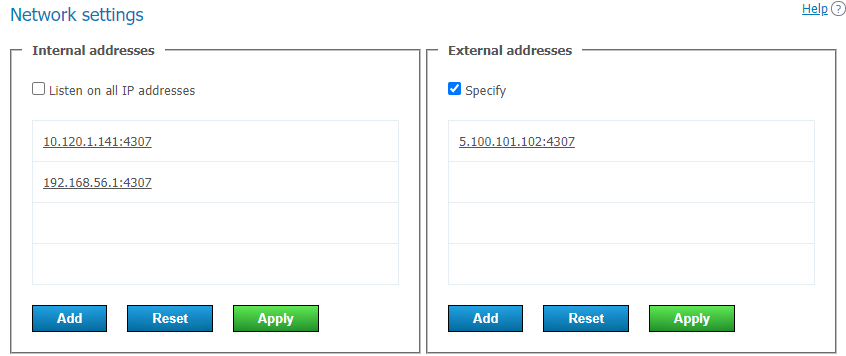
In the Internal addresses list, one will find the addresses and ports that the server will listen to for connections from client applications. These should be the addresses of the network interfaces on the machine where TrueConf Server is installed, or its internal DNS name, which resolves to one of the network interfaces by IP. When the box Listen on all IP addresses is checked (the default option), the list will be automatically created and will contain all such addresses, including virtual ones.
To edit the Internal addresses list, you will need to:
Uncheck the Listen on all IP addresses box.
To change the parameters for the specific connection, just click on the line with the selected address.
Use the buttons at the end of the list to add a new address and to save or discard changes.
Addresses from the External addresses list are added in an encrypted form to the name of TrueConf for Windows installer downloaded from the server guest page (refer to application settings). These addresses will be used when the application is launched for the first time. Users of your server and guests, who try to join a webinar, will be unable to connect to the server if the external address will be unavailable to them (however, they will be able to connect, if they specify a correct address in application settings). So, we suggest that in the External addresses list, you should specify the addresses accessible to all users both within the corporate network and from outside. This list can include addresses configured for forwarding to internal addresses, the IP address of your NAT, DNS name, or addresses to which you plan to migrate TrueConf Server in the future (so that the applications which were downloaded before, could connect to the server via the new IP address). If the server will be used only within a local network, this list will not be needed.
If you plan to migrate the server to another IP address, all you need to do is to add the new IP address to the External addresses list beforehand. This will help client apps to store the new address right after the next connection to the server in advance.
To edit the External addresses list, mark the Specify checkbox.
When the external address is adopted, go to the Web → Settings section section in the control panel and change the external address of the web page to a public IP (indicated in the External addresses list). Then restart the server so that external users can connect to it from outside.
This guide does not cover TCP port forwarding or DNS names. You can learn more about these topics in your network equipment manuals.
# Federation
Federation mode allows TrueConf Server users to make calls and participate in conferences with users of other TrueConf Server instances. Besides, it enables users from different servers to communicate in chats. Federation is available only in the full version of TrueConf Server (e.g., when purchasing additional licenses of any type). There is no limit on the number of servers that can be federated. The limits on group conferences will correspond to the limits applied to the TrueConf Server instance which initiated the connection.
Requirements for the correct work of federation:
The server has to be registered with an existing DNS name or you have to specify the real server address with the help of DNS SRV records.
Each federated server has to be accessible to another server by its DNS (FQDN) name, specified during registration, via the main port for the TrueConf protocol (4307 is selected by default). Moreover, it has to be accessible via an HTTPS port (443 is used by default). If a different HTTPS port is configured on one of the servers or a different port is selected for the communication protocol, access to this server should be configured via the selected port instead of the standard one.
Each federated server has to be available to all users of both servers (whose participation in calls and conferences is expected). Each server has to be accessible via an HTTPS port (443 is selected by default) by its domain name which should match the external server name specified during the registration.
IMPORTANT! If you are using a server which is below 5.4.0, it also has to be accessible to all federated users via the main port for the TrueConf protocol (4307 is used by default).
For more information on how a client application can find the server, refer to the section on the configuration of automatic connection.
Federation has to be configured on both servers to ensure that they are accessible to each other according to the rules mentioned above. To do it:
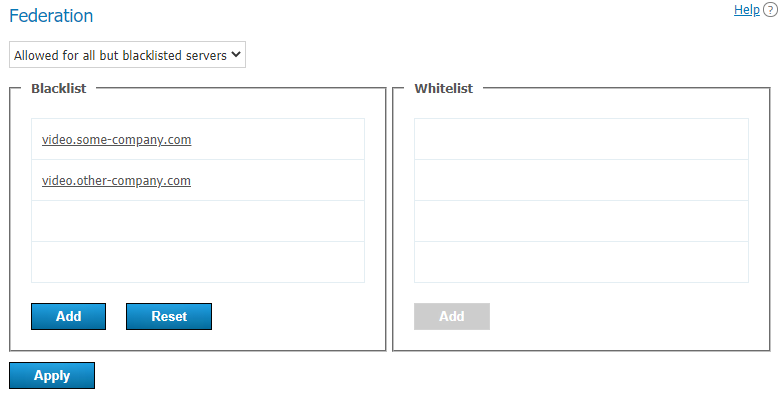
In the drop-down list, select the federation mode:
- Disabled
Allowed for whitelisted servers. In this mode, only TrueConf Server instances specified in the whitelist can be federated
Allowed for all but blacklisted servers. In this mode, all TrueConf Server instances can be federated except for those specified in the blacklist.
2. Enter the IP addresses or domain names (FQDNs) of the required servers into one of the lists (depending on the federation mode) and click Add.
IP addresses do not have to be specified for federation; only DNS (FQDN) names are needed. Besides, the masks containing an asterisk * are supported, for example, *.example.com, v*.example.com, example.*, *.example.*.
3. Click the Apply button to restart TrueConf Server and save changes.
# Federation use cases
Federated users can access the chat of a virtual room if they were added as participants when the room was created or edited, but not if they were added "on the fly" after the event had already started.
Let us take a look at some examples.
Case 1
To configure federation with a different TrueConf Server instance, e.g., videoserver.example.com, you will need to:
Add
videoserver.example.comto the white listActivate federation on the side of
videoserver.example.comin one of the following ways:Add the domain name of your server to the its white list
Allow federation with all the servers that have not been added to the black list (make sure that your server is not added to the black list).
3. Make sure that both servers and client applications connected to them, are accessible to each other by domain names.
Case 2
If the server videoserver.example.com is added to the blacklist, you will block all calls between users of your server and all users whose ID takes this form id@videoserver.example.com.
Connection to a conference in federation mode
Connection to a conference (including the cases when federation is used) is fully described in the "Conference page" section.
# TURN/STUN servers settings
If necessary, specify the STUN/TURN server addresses in the Network → TURN/STUN section for advanced configuration of NAT traversal.
To learn more about the work of WebRTC, refer to the article on our website.
When adding STUN/TURN, one should consider how this mechanism works:
TrueConf Server acts both as an authorization server and a WebRTC client (a conference participant) at the same time.
For the STUN or TURN server, one can choose various options in the Assigned for menu: for TrueConf Server, for a browser (WebRTC client), and for TrueConf client applications.
Depending on the role of STUN/TURN, its use will yield different results:
If the role of a STUN/TURN server is given to TrueConf Server, it will be possible for TrueConf Server to receive an external IP address.
If STUN/TURN is assigned for a WebRTC client, participants using browsers will be able to get an external IP address.
If STUN/TURN is assigned for native TrueConf applications, participants using the applications (desktop, mobile, TrueConf Room software endpoints, and TrueConf Kiosk application) will be able to get an external IP address.
4. The role of STUN/TURN can be given to TrueConf Server and the WebRTC client at the same time (both items are selected in the Assigned for drop-down list).
5. It is possible to add only 1 configuration in which the role of STUN/TURN is given to TrueConf Server.
6. There is no limit on the number of STUN/TURN servers assigned to a browser and TrueConf client applications.
If the STUN/TURN server role is assigned to users (a browser or a native application), these users will connect to the server in the following way:
At first, an attempt is made to connect via the local addresses of TrueConf Server.
If the attempt is unsuccessful, the browser client or native app tries to use external addresses obtained with the help of STUN servers.
If Step 2 also fails, the browser client attempts to establish a connection using TURN servers to proxy secure DTLS traffic.